
Easy SMTP Server 2.4 serial key or number

Easy SMTP Server 2.4 serial key or number
Updated by: 7504 DRAFT STANDARD
Errata Exist
Network Working Group J. Klensin Request for Comments: 5321 October 2008 Obsoletes: 2821 Updates: 1123 Category: Standards Track Simple Mail Transfer Protocol Status of This Memo This document specifies an Internet standards track protocol for the Internet community, and requests discussion and suggestions for improvements. Please refer to the current edition of the "Internet Official Protocol Standards" (STD 1) for the standardization state and status of this protocol. Distribution of this memo is unlimited. Abstract This document is a specification of the basic protocol for Internet electronic mail transport. It consolidates, updates, and clarifies several previous documents, making all or parts of most of them obsolete. It covers the SMTP extension mechanisms and best practices for the contemporary Internet, but does not provide details about particular extensions. Although SMTP was designed as a mail transport and delivery protocol, this specification also contains information that is important to its use as a "mail submission" protocol for "split-UA" (User Agent) mail reading systems and mobile environments. Klensin Standards Track [Page 1]
RFC 5321 SMTP October 2008 Table of Contents 1. Introduction . . . . . . . . . . . . . . . . . . . . . . . . . 51.1. Transport of Electronic Mail . . . . . . . . . . . . . . . 51.2. History and Context for This Document . . . . . . . . . . 51.3. Document Conventions . . . . . . . . . . . . . . . . . . . 62. The SMTP Model . . . . . . . . . . . . . . . . . . . . . . . . 72.1. Basic Structure . . . . . . . . . . . . . . . . . . . . . 72.2. The Extension Model . . . . . . . . . . . . . . . . . . . 92.2.1. Background . . . . . . . . . . . . . . . . . . . . . . 92.2.2. Definition and Registration of Extensions . . . . . . 102.2.3. Special Issues with Extensions . . . . . . . . . . . . 112.3. SMTP Terminology . . . . . . . . . . . . . . . . . . . . . 112.3.1. Mail Objects . . . . . . . . . . . . . . . . . . . . . 112.3.2. Senders and Receivers . . . . . . . . . . . . . . . . 122.3.3. Mail Agents and Message Stores . . . . . . . . . . . . 122.3.4. Host . . . . . . . . . . . . . . . . . . . . . . . . . 132.3.5. Domain Names . . . . . . . . . . . . . . . . . . . . . 132.3.6. Buffer and State Table . . . . . . . . . . . . . . . . 142.3.7. Commands and Replies . . . . . . . . . . . . . . . . . 142.3.8. Lines . . . . . . . . . . . . . . . . . . . . . . . . 142.3.9. Message Content and Mail Data . . . . . . . . . . . . 152.3.10. Originator, Delivery, Relay, and Gateway Systems . . . 152.3.11. Mailbox and Address . . . . . . . . . . . . . . . . . 152.4. General Syntax Principles and Transaction Model . . . . . 163. The SMTP Procedures: An Overview . . . . . . . . . . . . . . . 173.1. Session Initiation . . . . . . . . . . . . . . . . . . . . 183.2. Client Initiation . . . . . . . . . . . . . . . . . . . . 183.3. Mail Transactions . . . . . . . . . . . . . . . . . . . . 193.4. Forwarding for Address Correction or Updating . . . . . . 213.5. Commands for Debugging Addresses . . . . . . . . . . . . . 223.5.1. Overview . . . . . . . . . . . . . . . . . . . . . . . 223.5.2. VRFY Normal Response . . . . . . . . . . . . . . . . . 243.5.3. Meaning of VRFY or EXPN Success Response . . . . . . . 253.5.4. Semantics and Applications of EXPN . . . . . . . . . . 263.6. Relaying and Mail Routing . . . . . . . . . . . . . . . . 263.6.1. Source Routes and Relaying . . . . . . . . . . . . . . 263.6.2. Mail eXchange Records and Relaying . . . . . . . . . . 263.6.3. Message Submission Servers as Relays . . . . . . . . . 273.7. Mail Gatewaying . . . . . . . . . . . . . . . . . . . . . 283.7.1. Header Fields in Gatewaying . . . . . . . . . . . . . 283.7.2. Received Lines in Gatewaying . . . . . . . . . . . . . 293.7.3. Addresses in Gatewaying . . . . . . . . . . . . . . . 293.7.4. Other Header Fields in Gatewaying . . . . . . . . . . 293.7.5. Envelopes in Gatewaying . . . . . . . . . . . . . . . 303.8. Terminating Sessions and Connections . . . . . . . . . . . 303.9. Mailing Lists and Aliases . . . . . . . . . . . . . . . . 313.9.1. Alias . . . . . . . . . . . . . . . . . . . . . . . . 31Klensin Standards Track [Page 2]
RFC 5321 SMTP October 20083.9.2. List . . . . . . . . . . . . . . . . . . . . . . . . . 314. The SMTP Specifications . . . . . . . . . . . . . . . . . . . 324.1. SMTP Commands . . . . . . . . . . . . . . . . . . . . . . 324.1.1. Command Semantics and Syntax . . . . . . . . . . . . . 324.1.2. Command Argument Syntax . . . . . . . . . . . . . . . 414.1.3. Address Literals . . . . . . . . . . . . . . . . . . . 434.1.4. Order of Commands . . . . . . . . . . . . . . . . . . 444.1.5. Private-Use Commands . . . . . . . . . . . . . . . . . 464.2. SMTP Replies . . . . . . . . . . . . . . . . . . . . . . . 464.2.1. Reply Code Severities and Theory . . . . . . . . . . . 484.2.2. Reply Codes by Function Groups . . . . . . . . . . . . 504.2.3. Reply Codes in Numeric Order . . . . . . . . . . . . . 524.2.4. Reply Code 502 . . . . . . . . . . . . . . . . . . . . 53 4.2.5. Reply Codes after DATA and the Subsequent <CRLF>.<CRLF> . . . . . . . . . . . . . . . . . . . . 534.3. Sequencing of Commands and Replies . . . . . . . . . . . . 544.3.1. Sequencing Overview . . . . . . . . . . . . . . . . . 544.3.2. Command-Reply Sequences . . . . . . . . . . . . . . . 554.4. Trace Information . . . . . . . . . . . . . . . . . . . . 574.5. Additional Implementation Issues . . . . . . . . . . . . . 614.5.1. Minimum Implementation . . . . . . . . . . . . . . . . 614.5.2. Transparency . . . . . . . . . . . . . . . . . . . . . 624.5.3. Sizes and Timeouts . . . . . . . . . . . . . . . . . . 624.5.3.1. Size Limits and Minimums . . . . . . . . . . . . . 624.5.3.1.1. Local-part . . . . . . . . . . . . . . . . . . 634.5.3.1.2. Domain . . . . . . . . . . . . . . . . . . . . 634.5.3.1.3. Path . . . . . . . . . . . . . . . . . . . . . 634.5.3.1.4. Command Line . . . . . . . . . . . . . . . . . 634.5.3.1.5. Reply Line . . . . . . . . . . . . . . . . . . 634.5.3.1.6. Text Line . . . . . . . . . . . . . . . . . . 634.5.3.1.7. Message Content . . . . . . . . . . . . . . . 634.5.3.1.8. Recipients Buffer . . . . . . . . . . . . . . 644.5.3.1.9. Treatment When Limits Exceeded . . . . . . . . 644.5.3.1.10. Too Many Recipients Code . . . . . . . . . . . 644.5.3.2. Timeouts . . . . . . . . . . . . . . . . . . . . . 654.5.3.2.1. Initial 220 Message: 5 Minutes . . . . . . . . 654.5.3.2.2. MAIL Command: 5 Minutes . . . . . . . . . . . 654.5.3.2.3. RCPT Command: 5 Minutes . . . . . . . . . . . 654.5.3.2.4. DATA Initiation: 2 Minutes . . . . . . . . . . 664.5.3.2.5. Data Block: 3 Minutes . . . . . . . . . . . . 66 4.5.3.2.6. DATA Termination: 10 Minutes. . . . . . . . . 664.5.3.2.7. Server Timeout: 5 Minutes. . . . . . . . . . . 664.5.4. Retry Strategies . . . . . . . . . . . . . . . . . . . 664.5.5. Messages with a Null Reverse-Path . . . . . . . . . . 685. Address Resolution and Mail Handling . . . . . . . . . . . . . 695.1. Locating the Target Host . . . . . . . . . . . . . . . . . 695.2. IPv6 and MX Records . . . . . . . . . . . . . . . . . . . 716. Problem Detection and Handling . . . . . . . . . . . . . . . . 71Klensin Standards Track [Page 3]
RFC 5321 SMTP October 20086.1. Reliable Delivery and Replies by Email . . . . . . . . . . 716.2. Unwanted, Unsolicited, and "Attack" Messages . . . . . . . 726.3. Loop Detection . . . . . . . . . . . . . . . . . . . . . . 736.4. Compensating for Irregularities . . . . . . . . . . . . . 737. Security Considerations . . . . . . . . . . . . . . . . . . . 757.1. Mail Security and Spoofing . . . . . . . . . . . . . . . . 757.2. "Blind" Copies . . . . . . . . . . . . . . . . . . . . . . 767.3. VRFY, EXPN, and Security . . . . . . . . . . . . . . . . . 767.4. Mail Rerouting Based on the 251 and 551 Response Codes . . 777.5. Information Disclosure in Announcements . . . . . . . . . 777.6. Information Disclosure in Trace Fields . . . . . . . . . . 787.7. Information Disclosure in Message Forwarding . . . . . . . 787.8. Resistance to Attacks . . . . . . . . . . . . . . . . . . 787.9. Scope of Operation of SMTP Servers . . . . . . . . . . . . 788. IANA Considerations . . . . . . . . . . . . . . . . . . . . . 799. Acknowledgments . . . . . . . . . . . . . . . . . . . . . . . 8010. References . . . . . . . . . . . . . . . . . . . . . . . . . . 8110.1. Normative References . . . . . . . . . . . . . . . . . . . 8110.2. Informative References . . . . . . . . . . . . . . . . . . 82Appendix A. TCP Transport Service . . . . . . . . . . . . . . . . 85Appendix B. Generating SMTP Commands from RFC 822 Header Fields . . . . . . . . . . . . . . . . . . . . . . . 85Appendix C. Source Routes . . . . . . . . . . . . . . . . . . . . 86Appendix D. Scenarios . . . . . . . . . . . . . . . . . . . . . . 87D.1. A Typical SMTP Transaction Scenario . . . . . . . . . . . 88D.2. Aborted SMTP Transaction Scenario . . . . . . . . . . . . 89D.3. Relayed Mail Scenario . . . . . . . . . . . . . . . . . . 90D.4. Verifying and Sending Scenario . . . . . . . . . . . . . . 92Appendix E. Other Gateway Issues . . . . . . . . . . . . . . . . 92Appendix F. Deprecated Features of RFC 821 . . . . . . . . . . . 93F.1. TURN . . . . . . . . . . . . . . . . . . . . . . . . . . . 93F.2. Source Routing . . . . . . . . . . . . . . . . . . . . . . 93F.3. HELO . . . . . . . . . . . . . . . . . . . . . . . . . . . 93F.4. #-literals . . . . . . . . . . . . . . . . . . . . . . . . 94F.5. Dates and Years . . . . . . . . . . . . . . . . . . . . . 94F.6. Sending versus Mailing . . . . . . . . . . . . . . . . . . 94Klensin Standards Track [Page 4]
RFC 5321 SMTP October 20081. Introduction1.1. Transport of Electronic Mail The objective of the Simple Mail Transfer Protocol (SMTP) is to transfer mail reliably and efficiently. SMTP is independent of the particular transmission subsystem and requires only a reliable ordered data stream channel. While this document specifically discusses transport over TCP, other transports are possible. Appendices to RFC 821 [1] describe some of them. An important feature of SMTP is its capability to transport mail across multiple networks, usually referred to as "SMTP mail relaying" (see Section 3.6). A network consists of the mutually-TCP-accessible hosts on the public Internet, the mutually-TCP-accessible hosts on a firewall-isolated TCP/IP Intranet, or hosts in some other LAN or WAN environment utilizing a non-TCP transport-level protocol. Using SMTP, a process can transfer mail to another process on the same network or to some other network via a relay or gateway process accessible to both networks. In this way, a mail message may pass through a number of intermediate relay or gateway hosts on its path from sender to ultimate recipient. The Mail eXchanger mechanisms of the domain name system (RFC 1035 [2], RFC 974 [12], and Section 5 of this document) are used to identify the appropriate next-hop destination for a message being transported. 1.2. History and Context for This Document This document is a specification of the basic protocol for the Internet electronic mail transport. It consolidates, updates and clarifies, but does not add new or change existing functionality of the following: o the original SMTP (Simple Mail Transfer Protocol) specification of RFC 821 [1], o domain name system requirements and implications for mail transport from RFC 1035 [2] and RFC 974 [12], o the clarifications and applicability statements in RFC 1123 [3], and o material drawn from the SMTP Extension mechanisms in RFC 1869 [13]. Klensin Standards Track [Page 5]
RFC 5321 SMTP October 2008 o Editorial and clarification changes to RFC 2821 [14] to bring that specification to Draft Standard. It obsoletes RFC 821, RFC 974, RFC 1869, and RFC 2821 and updates RFC1123 (replacing the mail transport materials of RFC 1123). However, RFC 821 specifies some features that were not in significant use in the Internet by the mid-1990s and (in appendices) some additional transport models. Those sections are omitted here in the interest of clarity and brevity; readers needing them should refer to RFC 821. It also includes some additional material from RFC 1123 that required amplification. This material has been identified in multiple ways, mostly by tracking flaming on various lists and newsgroups and problems of unusual readings or interpretations that have appeared as the SMTP extensions have been deployed. Where this specification moves beyond consolidation and actually differs from earlier documents, it supersedes them technically as well as textually. Although SMTP was designed as a mail transport and delivery protocol, this specification also contains information that is important to its use as a "mail submission" protocol, as recommended for Post Office Protocol (POP) (RFC 937 [15], RFC 1939 [16]) and IMAP (RFC 3501 [17]). In general, the separate mail submission protocol specified in RFC 4409 [18] is now preferred to direct use of SMTP; more discussion of that subject appears in that document. Section 2.3 provides definitions of terms specific to this document. Except when the historical terminology is necessary for clarity, this document uses the current 'client' and 'server' terminology to identify the sending and receiving SMTP processes, respectively. A companion document, RFC 5322 [4], discusses message header sections and bodies and specifies formats and structures for them. 1.3. Document Conventions The key words "MUST", "MUST NOT", "REQUIRED", "SHALL", "SHALL NOT", "SHOULD", "SHOULD NOT", "RECOMMENDED", "MAY", and "OPTIONAL" in this document are to be interpreted as described in RFC 2119 [5]. As each of these terms was intentionally and carefully chosen to improve the interoperability of email, each use of these terms is to be treated as a conformance requirement. Because this document has a long history and to avoid the risk of various errors and of confusing readers and documents that point to this one, most examples and the domain names they contain are preserved from RFC 2821. Readers are cautioned that these are Klensin Standards Track [Page 6]
RFC 5321 SMTP October 2008 illustrative examples that should not actually be used in either code or configuration files. 2. The SMTP Model2.1. Basic Structure The SMTP design can be pictured as: +----------+ +----------+ +------+ | | | | | User |<-->| | SMTP | | +------+ | Client- |Commands/Replies| Server- | +------+ | SMTP |<-------------->| SMTP | +------+ | File |<-->| | and Mail | |<-->| File | |System| | | | | |System| +------+ +----------+ +----------+ +------+ SMTP client SMTP server When an SMTP client has a message to transmit, it establishes a two- way transmission channel to an SMTP server. The responsibility of an SMTP client is to transfer mail messages to one or more SMTP servers, or report its failure to do so. The means by which a mail message is presented to an SMTP client, and how that client determines the identifier(s) ("names") of the domain(s) to which mail messages are to be transferred, is a local matter, and is not addressed by this document. In some cases, the designated domain(s), or those determined by an SMTP client, will identify the final destination(s) of the mail message. In other cases, common with SMTP clients associated with implementations of the POP (RFC 937 [15], RFC 1939 [16]) or IMAP (RFC 3501 [17]) protocols, or when the SMTP client is inside an isolated transport service environment, the domain determined will identify an intermediate destination through which all mail messages are to be relayed. SMTP clients that transfer all traffic regardless of the target domains associated with the individual messages, or that do not maintain queues for retrying message transmissions that initially cannot be completed, may otherwise conform to this specification but are not considered fully-capable. Fully-capable SMTP implementations, including the relays used by these less capable ones, and their destinations, are expected to support all of the queuing, retrying, and alternate address functions discussed in this specification. In many situations and configurations, the less- capable clients discussed above SHOULD be using the message submission protocol (RFC 4409 [18]) rather than SMTP. Klensin Standards Track [Page 7]
RFC 5321 SMTP October 2008 The means by which an SMTP client, once it has determined a target domain, determines the identity of an SMTP server to which a copy of a message is to be transferred, and then performs that transfer, is covered by this document. To effect a mail transfer to an SMTP server, an SMTP client establishes a two-way transmission channel to that SMTP server. An SMTP client determines the address of an appropriate host running an SMTP server by resolving a destination domain name to either an intermediate Mail eXchanger host or a final target host. An SMTP server may be either the ultimate destination or an intermediate "relay" (that is, it may assume the role of an SMTP client after receiving the message) or "gateway" (that is, it may transport the message further using some protocol other than SMTP). SMTP commands are generated by the SMTP client and sent to the SMTP server. SMTP replies are sent from the SMTP server to the SMTP client in response to the commands. In other words, message transfer can occur in a single connection between the original SMTP-sender and the final SMTP-recipient, or can occur in a series of hops through intermediary systems. In either case, once the server has issued a success response at the end of the mail data, a formal handoff of responsibility for the message occurs: the protocol requires that a server MUST accept responsibility for either delivering the message or properly reporting the failure to do so (see Sections 6.1, 6.2, and 7.8, below). Once the transmission channel is established and initial handshaking is completed, the SMTP client normally initiates a mail transaction. Such a transaction consists of a series of commands to specify the originator and destination of the mail and transmission of the message content (including any lines in the header section or other structure) itself. When the same message is sent to multiple recipients, this protocol encourages the transmission of only one copy of the data for all recipients at the same destination (or intermediate relay) host. The server responds to each command with a reply; replies may indicate that the command was accepted, that additional commands are expected, or that a temporary or permanent error condition exists. Commands specifying the sender or recipients may include server- permitted SMTP service extension requests, as discussed in Section 2.2. The dialog is purposely lock-step, one-at-a-time, although this can be modified by mutually agreed upon extension requests such as command pipelining (RFC 2920 [19]). Once a given mail message has been transmitted, the client may either request that the connection be shut down or may initiate other mail Klensin Standards Track [Page 8]
RFC 5321 SMTP October 2008 transactions. In addition, an SMTP client may use a connection to an SMTP server for ancillary services such as verification of email addresses or retrieval of mailing list subscriber addresses. As suggested above, this protocol provides mechanisms for the transmission of mail. Historically, this transmission normally occurred directly from the sending user's host to the receiving user's host when the two hosts are connected to the same transport service. When they are not connected to the same transport service, transmission occurs via one or more relay SMTP servers. A very common case in the Internet today involves submission of the original message to an intermediate, "message submission" server, which is similar to a relay but has some additional properties; such servers are discussed in Section 2.3.10 and at some length in RFC 4409 [18]. An intermediate host that acts as either an SMTP relay or as a gateway into some other transmission environment is usually selected through the use of the domain name service (DNS) Mail eXchanger mechanism. Usually, intermediate hosts are determined via the DNS MX record, not by explicit "source" routing (see Section 5 and Appendix C and Appendix F.2). 2.2. The Extension Model2.2.1. Background In an effort that started in 1990, approximately a decade after RFC821 was completed, the protocol was modified with a "service extensions" model that permits the client and server to agree to utilize shared functionality beyond the original SMTP requirements. The SMTP extension mechanism defines a means whereby an extended SMTP client and server may recognize each other, and the server can inform the client as to the service extensions that it supports. Contemporary SMTP implementations MUST support the basic extension mechanisms. For instance, servers MUST support the EHLO command even if they do not implement any specific extensions and clients SHOULD preferentially utilize EHLO rather than HELO. (However, for compatibility with older conforming implementations, SMTP clients and servers MUST support the original HELO mechanisms as a fallback.) Unless the different characteristics of HELO must be identified for interoperability purposes, this document discusses only EHLO. SMTP is widely deployed and high-quality implementations have proven to be very robust. However, the Internet community now considers some services to be important that were not anticipated when the protocol was first designed. If support for those services is to be Klensin Standards Track [Page 9]
RFC 5321 SMTP October 2008 added, it must be done in a way that permits older implementations to continue working acceptably. The extension framework consists of: o The SMTP command EHLO, superseding the earlier HELO, o a registry of SMTP service extensions, o additional parameters to the SMTP MAIL and RCPT commands, and o optional replacements for commands defined in this protocol, such as for DATA in non-ASCII transmissions (RFC 3030 [20]). SMTP's strength comes primarily from its simplicity. Experience with many protocols has shown that protocols with few options tend towards ubiquity, whereas protocols with many options tend towards obscurity. Each and every extension, regardless of its benefits, must be carefully scrutinized with respect to its implementation, deployment, and interoperability costs. In many cases, the cost of extending the SMTP service will likely outweigh the benefit. 2.2.2. Definition and Registration of Extensions The IANA maintains a registry of SMTP service extensions. A corresponding EHLO keyword value is associated with each extension. Each service extension registered with the IANA must be defined in a formal Standards-Track or IESG-approved Experimental protocol document. The definition must include: o the textual name of the SMTP service extension; o the EHLO keyword value associated with the extension; o the syntax and possible values of parameters associated with the EHLO keyword value; o any additional SMTP verbs associated with the extension (additional verbs will usually be, but are not required to be, the same as the EHLO keyword value); o any new parameters the extension associates with the MAIL or RCPT verbs; o a description of how support for the extension affects the behavior of a server and client SMTP; and Klensin Standards Track [Page 10]
RFC 5321 SMTP October 2008 o the increment by which the extension is increasing the maximum length of the commands MAIL and/or RCPT, over that specified in this Standard. In addition, any EHLO keyword value starting with an upper or lower case "X" refers to a local SMTP service extension used exclusively through bilateral agreement. Keywords beginning with "X" MUST NOT be used in a registered service extension. Conversely, keyword values presented in the EHLO response that do not begin with "X" MUST correspond to a Standard, Standards-Track, or IESG-approved Experimental SMTP service extension registered with IANA. A conforming server MUST NOT offer non-"X"-prefixed keyword values that are not described in a registered extension. Additional verbs and parameter names are bound by the same rules as EHLO keywords; specifically, verbs beginning with "X" are local extensions that may not be registered or standardized. Conversely, verbs not beginning with "X" must always be registered. 2.2.3. Special Issues with Extensions Extensions that change fairly basic properties of SMTP operation are permitted. The text in other sections of this document must be understood in that context. In particular, extensions can change the minimum limits specified in Section 4.5.3, can change the ASCII character set requirement as mentioned above, or can introduce some optional modes of message handling. In particular, if an extension implies that the delivery path normally supports special features of that extension, and an intermediate SMTP system finds a next hop that does not support the required extension, it MAY choose, based on the specific extension and circumstances, to requeue the message and try later and/or try an alternate MX host. If this strategy is employed, the timeout to fall back to an unextended format (if one is available) SHOULD be less than the normal timeout for bouncing as undeliverable (e.g., if normal timeout is three days, the requeue timeout before attempting to transmit the mail without the extension might be one day). 2.3. SMTP Terminology2.3.1. Mail Objects SMTP transports a mail object. A mail object contains an envelope and content. The SMTP envelope is sent as a series of SMTP protocol units (described in Section 3). It consists of an originator address (to Klensin Standards Track [Page 11]
RFC 5321 SMTP October 2008 which error reports should be directed), one or more recipient addresses, and optional protocol extension material. Historically, variations on the reverse-path (originator) address specification command (MAIL) could be used to specify alternate delivery modes, such as immediate display; those variations have now been deprecated (see Appendix F and Appendix F.6). The SMTP content is sent in the SMTP DATA protocol unit and has two parts: the header section and the body. If the content conforms to other contemporary standards, the header section consists of a collection of header fields, each consisting of a header name, a colon, and data, structured as in the message format specification (RFC 5322 [4]); the body, if structured, is defined according to MIME (RFC 2045 [21]). The content is textual in nature, expressed using the US-ASCII repertoire [6]. Although SMTP extensions (such as "8BITMIME", RFC 1652 [22]) may relax this restriction for the content body, the content header fields are always encoded using the US-ASCII repertoire. Two MIME extensions (RFC 2047 [23] and RFC 2231 [24]) define an algorithm for representing header values outside the US- ASCII repertoire, while still encoding them using the US-ASCII repertoire. 2.3.2. Senders and Receivers In RFC 821, the two hosts participating in an SMTP transaction were described as the "SMTP-sender" and "SMTP-receiver". This document has been changed to reflect current industry terminology and hence refers to them as the "SMTP client" (or sometimes just "the client") and "SMTP server" (or just "the server"), respectively. Since a given host may act both as server and client in a relay situation, "receiver" and "sender" terminology is still used where needed for clarity. 2.3.3. Mail Agents and Message Stores Additional mail system terminology became common after RFC 821 was published and, where convenient, is used in this specification. In particular, SMTP servers and clients provide a mail transport service and therefore act as "Mail Transfer Agents" (MTAs). "Mail User Agents" (MUAs or UAs) are normally thought of as the sources and targets of mail. At the source, an MUA might collect mail to be transmitted from a user and hand it off to an MTA; the final ("delivery") MTA would be thought of as handing the mail off to an MUA (or at least transferring responsibility to it, e.g., by depositing the message in a "message store"). However, while these terms are used with at least the appearance of great precision in other environments, the implied boundaries between MUAs and MTAs often do not accurately match common, and conforming, practices with Klensin Standards Track [Page 12]
RFC 5321 SMTP October 2008 Internet mail. Hence, the reader should be cautious about inferring the strong relationships and responsibilities that might be implied if these terms were used elsewhere. 2.3.4. Host For the purposes of this specification, a host is a computer system attached to the Internet (or, in some cases, to a private TCP/IP network) and supporting the SMTP protocol. Hosts are known by names (see the next section); they SHOULD NOT be identified by numerical addresses, i.e., by address literals as described in Section 4.1.2. 2.3.5. Domain Names A domain name (or often just a "domain") consists of one or more components, separated by dots if more than one appears. In the case of a top-level domain used by itself in an email address, a single string is used without any dots. This makes the requirement, described in more detail below, that only fully-qualified domain names appear in SMTP transactions on the public Internet, particularly important where top-level domains are involved. These components ("labels" in DNS terminology, RFC 1035 [2]) are restricted for SMTP purposes to consist of a sequence of letters, digits, and hyphens drawn from the ASCII character set [6]. Domain names are used as names of hosts and of other entities in the domain name hierarchy. For example, a domain may refer to an alias (label of a CNAME RR) or the label of Mail eXchanger records to be used to deliver mail instead of representing a host name. See RFC 1035 [2] and Section 5 of this specification. The domain name, as described in this document and in RFC 1035 [2], is the entire, fully-qualified name (often referred to as an "FQDN"). A domain name that is not in FQDN form is no more than a local alias. Local aliases MUST NOT appear in any SMTP transaction. Only resolvable, fully-qualified domain names (FQDNs) are permitted when domain names are used in SMTP. In other words, names that can be resolved to MX RRs or address (i.e., A or AAAA) RRs (as discussed in Section 5) are permitted, as are CNAME RRs whose targets can be resolved, in turn, to MX or address RRs. Local nicknames or unqualified names MUST NOT be used. There are two exceptions to the rule requiring FQDNs: o The domain name given in the EHLO command MUST be either a primary host name (a domain name that resolves to an address RR) or, if the host has no name, an address literal, as described in Section 4.1.3 and discussed further in the EHLO discussion of Section 4.1.4. Klensin Standards Track [Page 13]
RFC 5321 SMTP October 2008 o The reserved mailbox name "postmaster" may be used in a RCPT command without domain qualification (see Section 4.1.1.3) and MUST be accepted if so used. 2.3.6. Buffer and State Table SMTP sessions are stateful, with both parties carefully maintaining a common view of the current state. In this document, we model this state by a virtual "buffer" and a "state table" on the server that may be used by the client to, for example, "clear the buffer" or "reset the state table", causing the information in the buffer to be discarded and the state to be returned to some previous state. 2.3.7. Commands and Replies SMTP commands and, unless altered by a service extension, message data, are transmitted from the sender to the receiver via the transmission channel in "lines". An SMTP reply is an acknowledgment (positive or negative) sent in "lines" from receiver to sender via the transmission channel in response to a command. The general form of a reply is a numeric completion code (indicating failure or success) usually followed by a text string. The codes are for use by programs and the text is usually intended for human users. RFC 3463 [25], specifies further structuring of the reply strings, including the use of supplemental and more specific completion codes (see also RFC 5248 [26]). 2.3.8. Lines Lines consist of zero or more data characters terminated by the sequence ASCII character "CR" (hex value 0D) followed immediately by ASCII character "LF" (hex value 0A). This termination sequence is denoted as <CRLF> in this document. Conforming implementations MUST NOT recognize or generate any other character or character sequence as a line terminator. Limits MAY be imposed on line lengths by servers (see Section 4). In addition, the appearance of "bare" "CR" or "LF" characters in text (i.e., either without the other) has a long history of causing problems in mail implementations and applications that use the mail system as a tool. SMTP client implementations MUST NOT transmit these characters except when they are intended as line terminators and then MUST, as indicated above, transmit them only as a <CRLF> sequence. Klensin Standards Track [Page 14]
RFC 5321 SMTP October 20082.3.9. Message Content and Mail Data The terms "message content" and "mail data" are used interchangeably in this document to describe the material transmitted after the DATA command is accepted and before the end of data indication is transmitted. Message content includes the message header section and the possibly structured message body. The MIME specification (RFC2045 [21]) provides the standard mechanisms for structured message bodies. 2.3.10. Originator, Delivery, Relay, and Gateway Systems This specification makes a distinction among four types of SMTP systems, based on the role those systems play in transmitting electronic mail. An "originating" system (sometimes called an SMTP originator) introduces mail into the Internet or, more generally, into a transport service environment. A "delivery" SMTP system is one that receives mail from a transport service environment and passes it to a mail user agent or deposits it in a message store that a mail user agent is expected to subsequently access. A "relay" SMTP system (usually referred to just as a "relay") receives mail from an SMTP client and transmits it, without modification to the message data other than adding trace information, to another SMTP server for further relaying or for delivery. A "gateway" SMTP system (usually referred to just as a "gateway") receives mail from a client system in one transport environment and transmits it to a server system in another transport environment. Differences in protocols or message semantics between the transport environments on either side of a gateway may require that the gateway system perform transformations to the message that are not permitted to SMTP relay systems. For the purposes of this specification, firewalls that rewrite addresses should be considered as gateways, even if SMTP is used on both sides of them (see RFC 2979 [27]). 2.3.11. Mailbox and Address As used in this specification, an "address" is a character string that identifies a user to whom mail will be sent or a location into which mail will be deposited. The term "mailbox" refers to that depository. The two terms are typically used interchangeably unless the distinction between the location in which mail is placed (the mailbox) and a reference to it (the address) is important. An address normally consists of user and domain specifications. The standard mailbox naming convention is defined to be "local-part@domain"; contemporary usage permits a much broader set of applications than simple "user names". Consequently, and due to a long history of problems when intermediate hosts have attempted to Klensin Standards Track [Page 15]
RFC 5321 SMTP October 2008 optimize transport by modifying them, the local-part MUST be interpreted and assigned semantics only by the host specified in the domain part of the address. 2.4. General Syntax Principles and Transaction Model SMTP commands and replies have a rigid syntax. All commands begin with a command verb. All replies begin with a three digit numeric code. In some commands and replies, arguments are required following the verb or reply code. Some commands do not accept arguments (after the verb), and some reply codes are followed, sometimes optionally, by free form text. In both cases, where text appears, it is separated from the verb or reply code by a space character. Complete definitions of commands and replies appear in Section 4. Verbs and argument values (e.g., "TO:" or "to:" in the RCPT command and extension name keywords) are not case sensitive, with the sole exception in this specification of a mailbox local-part (SMTP Extensions may explicitly specify case-sensitive elements). That is, a command verb, an argument value other than a mailbox local-part, and free form text MAY be encoded in upper case, lower case, or any mixture of upper and lower case with no impact on its meaning. The local-part of a mailbox MUST BE treated as case sensitive. Therefore, SMTP implementations MUST take care to preserve the case of mailbox local-parts. In particular, for some hosts, the user "smith" is different from the user "Smith". However, exploiting the case sensitivity of mailbox local-parts impedes interoperability and is discouraged. Mailbox domains follow normal DNS rules and are hence not case sensitive. A few SMTP servers, in violation of this specification (and RFC 821) require that command verbs be encoded by clients in upper case. Implementations MAY wish to employ this encoding to accommodate those servers. The argument clause consists of a variable-length character string ending with the end of the line, i.e., with the character sequence <CRLF>. The receiver will take no action until this sequence is received. The syntax for each command is shown with the discussion of that command. Common elements and parameters are shown in Section 4.1.2. Commands and replies are composed of characters from the ASCII character set [6]. When the transport service provides an 8-bit byte (octet) transmission channel, each 7-bit character is transmitted, right justified, in an octet with the high-order bit cleared to zero. More specifically, the unextended SMTP service provides 7-bit Klensin Standards Track [Page 16]
RFC 5321 SMTP October 2008 transport only. An originating SMTP client that has not successfully negotiated an appropriate extension with a particular server (see the next paragraph) MUST NOT transmit messages with information in the high-order bit of octets. If such messages are transmitted in violation of this rule, receiving SMTP servers MAY clear the high- order bit or reject the message as invalid. In general, a relay SMTP SHOULD assume that the message content it has received is valid and, assuming that the envelope permits doing so, relay it without inspecting that content. Of course, if the content is mislabeled and the data path cannot accept the actual content, this may result in the ultimate delivery of a severely garbled message to the recipient. Delivery SMTP systems MAY reject such messages, or return them as undeliverable, rather than deliver them. In the absence of a server- offered extension explicitly permitting it, a sending SMTP system is not permitted to send envelope commands in any character set other than US-ASCII. Receiving systems SHOULD reject such commands, normally using "500 syntax error - invalid character" replies. 8-bit message content transmission MAY be requested of the server by a client using extended SMTP facilities, notably the "8BITMIME" extension, RFC 1652 [22]. 8BITMIME SHOULD be supported by SMTP servers. However, it MUST NOT be construed as authorization to transmit unrestricted 8-bit material, nor does 8BITMIME authorize transmission of any envelope material in other than ASCII. 8BITMIME MUST NOT be requested by senders for material with the high bit on that is not in MIME format with an appropriate content-transfer encoding; servers MAY reject such messages. The metalinguistic notation used in this document corresponds to the "Augmented BNF" used in other Internet mail system documents. The reader who is not familiar with that syntax should consult the ABNF specification in RFC 5234 [7]. Metalanguage terms used in running text are surrounded by pointed brackets (e.g., <CRLF>) for clarity. The reader is cautioned that the grammar expressed in the metalanguage is not comprehensive. There are many instances in which provisions in the text constrain or otherwise modify the syntax or semantics implied by the grammar. 3. The SMTP Procedures: An Overview This section contains descriptions of the procedures used in SMTP: session initiation, mail transaction, forwarding mail, verifying mailbox names and expanding mailing lists, and opening and closing exchanges. Comments on relaying, a note on mail domains, and a discussion of changing roles are included at the end of this section. Several complete scenarios are presented in Appendix D. Klensin Standards Track [Page 17]
RFC 5321 SMTP October 20083.1. Session Initiation An SMTP session is initiated when a client opens a connection to a server and the server responds with an opening message. SMTP server implementations MAY include identification of their software and version information in the connection greeting reply after the 220 code, a practice that permits more efficient isolation and repair of any problems. Implementations MAY make provision for SMTP servers to disable the software and version announcement where it causes security concerns. While some systems also identify their contact point for mail problems, this is not a substitute for maintaining the required "postmaster" address (see Section 4). The SMTP protocol allows a server to formally reject a mail session while still allowing the initial connection as follows: a 554 response MAY be given in the initial connection opening message instead of the 220. A server taking this approach MUST still wait for the client to send a QUIT (see Section 4.1.1.10) before closing the connection and SHOULD respond to any intervening commands with "503 bad sequence of commands". Since an attempt to make an SMTP connection to such a system is probably in error, a server returning a 554 response on connection opening SHOULD provide enough information in the reply text to facilitate debugging of the sending system. 3.2. Client Initiation Once the server has sent the greeting (welcoming) message and the client has received it, the client normally sends the EHLO command to the server, indicating the client's identity. In addition to opening the session, use of EHLO indicates that the client is able to process service extensions and requests that the server provide a list of the extensions it supports. Older SMTP systems that are unable to support service extensions, and contemporary clients that do not require service extensions in the mail session being initiated, MAY use HELO instead of EHLO. Servers MUST NOT return the extended EHLO- style response to a HELO command. For a particular connection attempt, if the server returns a "command not recognized" response to EHLO, the client SHOULD be able to fall back and send HELO. In the EHLO command, the host sending the command identifies itself; the command may be interpreted as saying "Hello, I am <domain>" (and, in the case of EHLO, "and I support service extension requests"). Klensin Standards Track [Page 18]
RFC 5321 SMTP October 20083.3. Mail Transactions There are three steps to SMTP mail transactions. The transaction starts with a MAIL command that gives the sender identification. (In general, the MAIL command may be sent only when no mail transaction is in progress; see Section 4.1.4.) A series of one or more RCPT commands follows, giving the receiver information. Then, a DATA command initiates transfer of the mail data and is terminated by the "end of mail" data indicator, which also confirms the transaction. The first step in the procedure is the MAIL command. MAIL FROM:<reverse-path> [SP <mail-parameters> ] <CRLF> This command tells the SMTP-receiver that a new mail transaction is starting and to reset all its state tables and buffers, including any recipients or mail data. The <reverse-path> portion of the first or only argument contains the source mailbox (between "<" and ">" brackets), which can be used to report errors (see Section 4.2 for a discussion of error reporting). If accepted, the SMTP server returns a "250 OK" reply. If the mailbox specification is not acceptable for some reason, the server MUST return a reply indicating whether the failure is permanent (i.e., will occur again if the client tries to send the same address again) or temporary (i.e., the address might be accepted if the client tries again later). Despite the apparent scope of this requirement, there are circumstances in which the acceptability of the reverse-path may not be determined until one or more forward-paths (in RCPT commands) can be examined. In those cases, the server MAY reasonably accept the reverse-path (with a 250 reply) and then report problems after the forward-paths are received and examined. Normally, failures produce 550 or 553 replies. Historically, the <reverse-path> was permitted to contain more than just a mailbox; however, contemporary systems SHOULD NOT use source routing (see Appendix C). The optional <mail-parameters> are associated with negotiated SMTP service extensions (see Section 2.2). The second step in the procedure is the RCPT command. This step of the procedure can be repeated any number of times. RCPT TO:<forward-path> [ SP <rcpt-parameters> ] <CRLF> The first or only argument to this command includes a forward-path (normally a mailbox and domain, always surrounded by "<" and ">" brackets) identifying one recipient. If accepted, the SMTP server returns a "250 OK" reply and stores the forward-path. If the Klensin Standards Track [Page 19]
RFC 5321 SMTP October 2008 recipient is known not to be a deliverable address, the SMTP server returns a 550 reply, typically with a string such as "no such user - " and the mailbox name (other circumstances and reply codes are possible). The <forward-path> can contain more than just a mailbox. Historically, the <forward-path> was permitted to contain a source routing list of hosts and the destination mailbox; however, contemporary SMTP clients SHOULD NOT utilize source routes (see Appendix C). Servers MUST be prepared to encounter a list of source routes in the forward-path, but they SHOULD ignore the routes or MAY decline to support the relaying they imply. Similarly, servers MAY decline to accept mail that is destined for other hosts or systems. These restrictions make a server useless as a relay for clients that do not support full SMTP functionality. Consequently, restricted- capability clients MUST NOT assume that any SMTP server on the Internet can be used as their mail processing (relaying) site. If a RCPT command appears without a previous MAIL command, the server MUST return a 503 "Bad sequence of commands" response. The optional <rcpt-parameters> are associated with negotiated SMTP service extensions (see Section 2.2). Since it has been a common source of errors, it is worth noting that spaces are not permitted on either side of the colon following FROM in the MAIL command or TO in the RCPT command. The syntax is exactly as given above. The third step in the procedure is the DATA command (or some alternative specified in a service extension). DATA <CRLF> If accepted, the SMTP server returns a 354 Intermediate reply and considers all succeeding lines up to but not including the end of mail data indicator to be the message text. When the end of text is successfully received and stored, the SMTP-receiver sends a "250 OK" reply. Since the mail data is sent on the transmission channel, the end of mail data must be indicated so that the command and reply dialog can be resumed. SMTP indicates the end of the mail data by sending a line containing only a "." (period or full stop). A transparency procedure is used to prevent this from interfering with the user's text (see Section 4.5.2). The end of mail data indicator also confirms the mail transaction and tells the SMTP server to now process the stored recipients and mail Klensin Standards Track [Page 20]
RFC 5321 SMTP October 2008 data. If accepted, the SMTP server returns a "250 OK" reply. The DATA command can fail at only two points in the protocol exchange: If there was no MAIL, or no RCPT, command, or all such commands were rejected, the server MAY return a "command out of sequence" (503) or "no valid recipients" (554) reply in response to the DATA command. If one of those replies (or any other 5yz reply) is received, the client MUST NOT send the message data; more generally, message data MUST NOT be sent unless a 354 reply is received. If the verb is initially accepted and the 354 reply issued, the DATA command should fail only if the mail transaction was incomplete (for example, no recipients), if resources were unavailable (including, of course, the server unexpectedly becoming unavailable), or if the server determines that the message should be rejected for policy or other reasons. However, in practice, some servers do not perform recipient verification until after the message text is received. These servers SHOULD treat a failure for one or more recipients as a "subsequent failure" and return a mail message as discussed in Section 6 and, in particular, in Section 6.1. Using a "550 mailbox not found" (or equivalent) reply code after the data are accepted makes it difficult or impossible for the client to determine which recipients failed. When the RFC 822 format ([28], [4]) is being used, the mail data include the header fields such as those named Date, Subject, To, Cc, and From. Server SMTP systems SHOULD NOT reject messages based on perceived defects in the RFC 822 or MIME (RFC 2045 [21]) message header section or message body. In particular, they MUST NOT reject messages in which the numbers of Resent-header fields do not match or Resent-to appears without Resent-from and/or Resent-date. Mail transaction commands MUST be used in the order discussed above. 3.4. Forwarding for Address Correction or Updating Forwarding support is most often required to consolidate and simplify addresses within, or relative to, some enterprise and less frequently to establish addresses to link a person's prior address with a current one. Silent forwarding of messages (without server notification to the sender), for security or non-disclosure purposes, is common in the contemporary Internet. In both the enterprise and the "new address" cases, information hiding (and sometimes security) considerations argue against exposure of the "final" address through the SMTP protocol as a side effect of the forwarding activity. This may be especially important when the Klensin Standards Track [Page 21]
RFC 5321 SMTP October 2008 final address may not even be reachable by the sender. Consequently, the "forwarding" mechanisms described in Section 3.2 of RFC 821, and especially the 251 (corrected destination) and 551 reply codes from RCPT must be evaluated carefully by implementers and, when they are available, by those configuring systems (see also Section 7.4). In particular: o Servers MAY forward messages when they are aware of an address change. When they do so, they MAY either provide address-updating information with a 251 code, or may forward "silently" and return a 250 code. However, if a 251 code is used, they MUST NOT assume that the client will actually update address information or even return that information to the user. Alternately, o Servers MAY reject messages or return them as non-deliverable when they cannot be delivered precisely as addressed. When they do so, they MAY either provide address-updating information with a 551 code, or may reject the message as undeliverable with a 550 code and no address-specific information. However, if a 551 code is used, they MUST NOT assume that the client will actually update address information or even return that information to the user. SMTP server implementations that support the 251 and/or 551 reply codes SHOULD provide configuration mechanisms so that sites that conclude that they would undesirably disclose information can disable or restrict their use. 3.5. Commands for Debugging Addresses3.5.1. Overview SMTP provides commands to verify a user name or obtain the content of a mailing list. This is done with the VRFY and EXPN commands, which have character string arguments. Implementations SHOULD support VRFY and EXPN (however, see Section 3.5.2 and Section 7.3). For the VRFY command, the string is a user name or a user name and domain (see below). If a normal (i.e., 250) response is returned, the response MAY include the full name of the user and MUST include the mailbox of the user. It MUST be in either of the following forms: User Name <local-part@domain> local-part@domain Klensin Standards Track [Page 22]
RFC 5321 SMTP October 2008 When a name that is the argument to VRFY could identify more than one mailbox, the server MAY either note the ambiguity or identify the alternatives. In other words, any of the following are legitimate responses to VRFY: 553 User ambiguous or 553- Ambiguous; Possibilities are 553-Joe Smith <jsmith@foo.com> 553-Harry Smith <hsmith@foo.com> 553 Melvin Smith <dweep@foo.com> or 553-Ambiguous; Possibilities 553- <jsmith@foo.com> 553- <hsmith@foo.com> 553 <dweep@foo.com> Under normal circumstances, a client receiving a 553 reply would be expected to expose the result to the user. Use of exactly the forms given, and the "user ambiguous" or "ambiguous" keywords, possibly supplemented by extended reply codes, such as those described in RFC3463 [25], will facilitate automated translation into other languages as needed. Of course, a client that was highly automated or that was operating in another language than English might choose to try to translate the response to return some other indication to the user than the literal text of the reply, or to take some automated action such as consulting a directory service for additional information before reporting to the user. For the EXPN command, the string identifies a mailing list, and the successful (i.e., 250) multiline response MAY include the full name of the users and MUST give the mailboxes on the mailing list. In some hosts, the distinction between a mailing list and an alias for a single mailbox is a bit fuzzy, since a common data structure may hold both types of entries, and it is possible to have mailing lists containing only one mailbox. If a request is made to apply VRFY to a mailing list, a positive response MAY be given if a message so addressed would be delivered to everyone on the list, otherwise an error SHOULD be reported (e.g., "550 That is a mailing list, not a user" or "252 Unable to verify members of mailing list"). If a request is made to expand a user name, the server MAY return a Klensin Standards Track [Page 23]
RFC 5321 SMTP October 2008 positive response consisting of a list containing one name, or an error MAY be reported (e.g., "550 That is a user name, not a mailing list"). In the case of a successful multiline reply (normal for EXPN), exactly one mailbox is to be specified on each line of the reply. The case of an ambiguous request is discussed above. "User name" is a fuzzy term and has been used deliberately. An implementation of the VRFY or EXPN commands MUST include at least recognition of local mailboxes as "user names". However, since current Internet practice often results in a single host handling mail for multiple domains, hosts, especially hosts that provide this functionality, SHOULD accept the "local-part@domain" form as a "user name"; hosts MAY also choose to recognize other strings as "user names". The case of expanding a mailbox list requires a multiline reply, such as: C: EXPN Example-People S: 250-Jon Postel <Postel@isi.edu> S: 250-Fred Fonebone <Fonebone@physics.foo-u.edu> S: 250 Sam Q. Smith <SQSmith@specific.generic.com> or C: EXPN Executive-Washroom-List S: 550 Access Denied to You. The character string arguments of the VRFY and EXPN commands cannot be further restricted due to the variety of implementations of the user name and mailbox list concepts. On some systems, it may be appropriate for the argument of the EXPN command to be a file name for a file containing a mailing list, but again there are a variety of file naming conventions in the Internet. Similarly, historical variations in what is returned by these commands are such that the response SHOULD be interpreted very carefully, if at all, and SHOULD generally only be used for diagnostic purposes. 3.5.2. VRFY Normal Response When normal (2yz or 551) responses are returned from a VRFY or EXPN request, the reply MUST include the <Mailbox> name using a "<local-part@domain>" construction, where "domain" is a fully- qualified domain name. In circumstances exceptional enough to justify violating the intent of this specification, free-form text MAY be returned. In order to facilitate parsing by both computers Klensin Standards Track [Page 24]
RFC 5321 SMTP October 2008 and people, addresses SHOULD appear in pointed brackets. When addresses, rather than free-form debugging information, are returned, EXPN and VRFY MUST return only valid domain addresses that are usable in SMTP RCPT commands. Consequently, if an address implies delivery to a program or other system, the mailbox name used to reach that target MUST be given. Paths (explicit source routes) MUST NOT be returned by VRFY or EXPN. Server implementations SHOULD support both VRFY and EXPN. For security reasons, implementations MAY provide local installations a way to disable either or both of these commands through configuration options or the equivalent (see Section 7.3). When these commands are supported, they are not required to work across relays when relaying is supported. Since they were both optional in RFC 821, but VRFY was made mandatory in RFC 1123 [3], if EXPN is supported, it MUST be listed as a service extension in an EHLO response. VRFY MAY be listed as a convenience but, since support for it is required, SMTP clients are not required to check for its presence on the extension list before using it. 3.5.3. Meaning of VRFY or EXPN Success Response A server MUST NOT return a 250 code in response to a VRFY or EXPN command unless it has actually verified the address. In particular, a server MUST NOT return 250 if all it has done is to verify that the syntax given is valid. In that case, 502 (Command not implemented) or 500 (Syntax error, command unrecognized) SHOULD be returned. As stated elsewhere, implementation (in the sense of actually validating addresses and returning information) of VRFY and EXPN are strongly recommended. Hence, implementations that return 500 or 502 for VRFY are not in full compliance with this specification. There may be circumstances where an address appears to be valid but cannot reasonably be verified in real time, particularly when a server is acting as a mail exchanger for another server or domain. "Apparent validity", in this case, would normally involve at least syntax checking and might involve verification that any domains specified were ones to which the host expected to be able to relay mail. In these situations, reply code 252 SHOULD be returned. These cases parallel the discussion of RCPT verification in Section 2.1. Similarly, the discussion in Section 3.4 applies to the use of reply codes 251 and 551 with VRFY (and EXPN) to indicate addresses that are recognized but that would be forwarded or rejected were mail received for them. Implementations generally SHOULD be more aggressive about address verification in the case of VRFY than in the case of RCPT, even if it takes a little longer to do so. Klensin Standards Track [Page 25]
RFC 5321 SMTP October 20083.5.4. Semantics and Applications of EXPN EXPN is often very useful in debugging and understanding problems with mailing lists and multiple-target-address aliases. Some systems have attempted to use source expansion of mailing lists as a means of eliminating duplicates. The propagation of aliasing systems with mail on the Internet for hosts (typically with MX and CNAME DNS records), for mailboxes (various types of local host aliases), and in various proxying arrangements has made it nearly impossible for these strategies to work consistently, and mail systems SHOULD NOT attempt them. 3.6. Relaying and Mail Routing3.6.1. Source Routes and Relaying In general, the availability of Mail eXchanger records in the domain name system (RFC 1035 [2], RFC 974 [12]) makes the use of explicit source routes in the Internet mail system unnecessary. Many historical problems with the interpretation of explicit source routes have made their use undesirable. SMTP clients SHOULD NOT generate explicit source routes except under unusual circumstances. SMTP servers MAY decline to act as mail relays or to accept addresses that specify source routes. When route information is encountered, SMTP servers MAY ignore the route information and simply send to the final destination specified as the last element in the route and SHOULD do so. There has been an invalid practice of using names that do not appear in the DNS as destination names, with the senders counting on the intermediate hosts specified in source routing to resolve any problems. If source routes are stripped, this practice will cause failures. This is one of several reasons why SMTP clients MUST NOT generate invalid source routes or depend on serial resolution of names. When source routes are not used, the process described in RFC 821 for constructing a reverse-path from the forward-path is not applicable and the reverse-path at the time of delivery will simply be the address that appeared in the MAIL command. 3.6.2. Mail eXchange Records and Relaying A relay SMTP server is usually the target of a DNS MX record that designates it, rather than the final delivery system. The relay server may accept or reject the task of relaying the mail in the same way it accepts or rejects mail for a local user. If it accepts the task, it then becomes an SMTP client, establishes a transmission channel to the next SMTP server specified in the DNS (according to the rules in Section 5), and sends it the mail. If it declines to Klensin Standards Track [Page 26]
RFC 5321 SMTP October 2008 relay mail to a particular address for policy reasons, a 550 response SHOULD be returned. This specification does not deal with the verification of return paths for use in delivery notifications. Recent work, such as that on SPF [29] and DKIM [30] [31], has been done to provide ways to ascertain that an address is valid or belongs to the person who actually sent the message. A server MAY attempt to verify the return path before using its address for delivery notifications, but methods of doing so are not defined here nor is any particular method recommended at this time. 3.6.3. Message Submission Servers as Relays Many mail-sending clients exist, especially in conjunction with facilities that receive mail via POP3 or IMAP, that have limited capability to support some of the requirements of this specification, such as the ability to queue messages for subsequent delivery attempts. For these clients, it is common practice to make private arrangements to send all messages to a single server for processing and subsequent distribution. SMTP, as specified here, is not ideally suited for this role. A standardized mail submission protocol has been developed that is gradually superseding practices based on SMTP (see RFC 4409 [18]). In any event, because these arrangements are private and fall outside the scope of this specification, they are not described here. It is important to note that MX records can point to SMTP servers that act as gateways into other environments, not just SMTP relays and final delivery systems; see Sections 3.7 and 5. If an SMTP server has accepted the task of relaying the mail and later finds that the destination is incorrect or that the mail cannot be delivered for some other reason, then it MUST construct an "undeliverable mail" notification message and send it to the originator of the undeliverable mail (as indicated by the reverse- path). Formats specified for non-delivery reports by other standards (see, for example, RFC 3461 [32] and RFC 3464 [33]) SHOULD be used if possible. This notification message must be from the SMTP server at the relay host or the host that first determines that delivery cannot be accomplished. Of course, SMTP servers MUST NOT send notification messages about problems transporting notification messages. One way to prevent loops in error reporting is to specify a null reverse-path in the MAIL command of a notification message. When such a message is transmitted, the reverse-path MUST be set to null (see Klensin Standards Track [Page 27]
RFC 5321 SMTP October 2008Section 4.5.5 for additional discussion). A MAIL command with a null reverse-path appears as follows: MAIL FROM:<> As discussed in Section 6.4, a relay SMTP has no need to inspect or act upon the header section or body of the message data and MUST NOT do so except to add its own "Received:" header field (Section 4.4) and, optionally, to attempt to detect looping in the mail system (see Section 6.3). Of course, this prohibition also applies to any modifications of these header fields or text (see also Section 7.9). 3.7. Mail Gatewaying While the relay function discussed above operates within the Internet SMTP transport service environment, MX records or various forms of explicit routing may require that an intermediate SMTP server perform a translation function between one transport service and another. As discussed in Section 2.3.10, when such a system is at the boundary between two transport service environments, we refer to it as a "gateway" or "gateway SMTP". Gatewaying mail between different mail environments, such as different mail formats and protocols, is complex and does not easily yield to standardization. However, some general requirements may be given for a gateway between the Internet and another mail environment. 3.7.1. Header Fields in Gatewaying Header fields MAY be rewritten when necessary as messages are gatewayed across mail environment boundaries. This may involve inspecting the message body or interpreting the local-part of the destination address in spite of the prohibitions in Section 6.4. Other mail systems gatewayed to the Internet often use a subset of the RFC 822 header section or provide similar functionality with a different syntax, but some of these mail systems do not have an equivalent to the SMTP envelope. Therefore, when a message leaves the Internet environment, it may be necessary to fold the SMTP envelope information into the message header section. A possible solution would be to create new header fields to carry the envelope information (e.g., "X-SMTP-MAIL:" and "X-SMTP-RCPT:"); however, this would require changes in mail programs in foreign environments and might risk disclosure of private information (see Section 7.2). Klensin Standards Track [Page 28]
RFC 5321 SMTP October 20083.7.2. Received Lines in Gatewaying
Plesk Documentation and Help Portal
Specifies the mail relay mode for the mail server.
If parameter is used, requires the opion.
To set the Plesk mail server relaying mode to “authorization is required” ():
pleskbinmailserver--set-relay auth -auth-type both
To restrict the maximum message size that can be accepted by the mail server to 2 M:
pleskbinmailserver--set-max-letter-size 2M
To limit the number of concurrent connections to the mail server to 100:
pleskbinmailserver--set-max-connections 100
To limit the number of concurrent connections to the mail server from a single IP address to 5:
pleskbinmailserver--set-max-connections-per-ip 5
To enable MAPS spam protection on the mail server:
pleskbinmailserver--set-maps-status true
To add domain names maps1.example.com and maps2.example.com to the MAPS spam protection list:
pleskbinmailserver--add-maps-zone maps1.example.com,maps2.example.com
To enable MAPS spam protection for domain names maps1.example.com and maps2.example.com:
pleskbinmailserver--set-maps-zone maps1.example.com,maps2.example.com
To remove domain names maps1.example.com and maps2.example.com from the MAPS spam protection list:
pleskbinmailserver--remove-maps-zone maps1.example.com,maps2.example.com
Specifies the mail user login name format for accessing mail accounts by means of the POP3 or IMAP protocols.
- - only login names in the <user@example.com> (the “full” format) are allowed
- - login names in both <user> (the “short” format) and <user@example.com> (the “full” format) are allowed
Is set to by default.
To allow using both the “short” and “full” login name formats for mail users to access their mail accounts by means of the POP3 or IMAP protocols on the mail server:
pleskbinmailserver--set-account-type both
To enable checking of mail user passwords against the password dictionary to prevent users from setting simple passwords:
pleskbinmailserver--use-vocabulary true
To add domain names example.org and sample.example.net to the black list of mail server:
pleskbinmailserver--add-to-black-list example.org,sample.example.net
To remove domain names sample.example.org and forum.example.net from the mail server black list:
pleskbinmailserver--remove-from-black-list sample.example.org,forum.example.net
To add 192.0.2.0/24 and 192.0.2.3/16 to the mail server white list:
pleskbinmailserver--add-to-white-list 192.0.2.0/24,10.0.0.0/24
To remove 192.0.2.0/24 and 192.0.2.4/16 from the mail server white list:
pleskbinmailserver--remove-from-white-list 192.0.2.0/24,10.0.0.0/24
To enable the Odin Premium antivirus on the mail server:
pleskbinmailserver--set-virusfilter drweb
Updates the Sender Policy Framework (SPF) settings.
Note: SPF cannot be disabled if DMARC spam protection is enabled.
To enable the SPF spam protection on the mail server:
pleskbinmailserver--update-spf -spf-status true
Enables DMARC spam protection.
Note: This command can be used only if DKIM and SPF spam protection are enabled. Otherwise, the error message will be displayed.
To enable DMARC spam protection for incoming mail on the mail server:
pleskbinmailserver--enable-dmarc
To disable DMARC spam protection for incoming mail on the mail server:
pleskbinmailserver--disable-dmarc
To enable message submission on all IP addresses:
pleskbinmailserver--set-message-submission true
Allows/Prohibits using DKIM spam protection method to sign outgoing mail.
Is by default.
To enable signing of outgoing mail on the mail server:
pleskbinmailserver--sign-outgoing-mail true
Allows/Prohibits using DKIM spam protection method to verify incoming mail.
Is by default.
Note: DKIM cannot be disabled for incoming mail if DMARC spam protection is enabled.
To enable verifying incoming mail on the mail server:
pleskbinmailserver--verify-incoming-mail true
Enables/Disables the selected webmail client.
Requires the option.
To enable Horde webmail on the mail server:
pleskbinmailserver--update-webmail horde -state true
Displays mail server settings. The following modes are available:
- - displays various mail server settings except for the mail server black and white lists contents and the Sender Policy Framework (SPF) settings.
- - displays the mail server black list content
- - displays the mail server white list content
- - displays the SPF settings.
- - displays the webmail software used in Plesk and its status.
To view the SPF settings:
pleskbinmailserver--info spf
or
pleskbinmailserver-ispf
To remove the messages in the mail queue:
pleskbinmailserver--clean-mail-queue
Registers an additional (external) webmail service with the Plesk so that you can provide your users with access to it.
Requires the and the options.
To learn more about registering additional webmail services with the Plesk, refer to Administrator’s Guide at http://docs.plesk.com/en-US/17.0/administrator-guide/mail/webmail-software
To register an external webmail service called ExampleMail at URL mail.example.com:
pleskbinmailserver--add-external-webmail -webmail-name ExampleMail -webmail-url mail.example.com
To change the URL for the webmail record ExampleMail to mail2.example.com:
pleskbinmailserver--update-external-webmail "ExampleMail" -webmail-url mail2.example.com
To change the name for the external webmail service ExampleMail to SampleMail:
pleskbinmailserver--update-external-webmail "ExampleMail" -webmail-name "SampleMail"
To remove the external webmail service record ExampleMail:
pleskbinmailserver--remove-external-webmail "ExampleMail"
Updates the settings of an external SMTP server for outgoing mail.
Note that to use an external SMTP server, you should install a special client through Tools & Settings > Updates > Mail hosting features > Different mail servers.
To update the external SMTP server settings:
pleskbinmailserver--update-smtp-settings -mail-notifications true -smtp-host 123.123.123.123 -smtp-port 587 -smtp-login jdoe -smtp-password sample -smtp-tls true -smtp-allow-users true
To turn on the usage of limitations on outgoing mail from the Plesk server:
pleskbinmailserver--enable-outgoing-antispam
To turn off the usage of limitations on outgoing mail from the Plesk server:
pleskbinmailserver--disable-outgoing-antispam
To set the default value for the limit on outgoing email messages from an email address:
pleskbinmailserver--set-outgoing-messages-mbox-limit 5
To set the default value for the limit on outgoing email messages from a domain:
pleskbinmailserver--set-outgoing-messages-domain-limit 10
To set the default value for the limit on outgoing email messages from a subscription:
pleskbinmailserver--set-outgoing-messages-subscription-limit 50
To prohibit PHP scripts send outgoing mail from the Plesk server using sendmail:
pleskbinmailserver--set-outgoing-messages-enable-sendmail false
To make Plesk calculate reports on outgoing mail using the data for the last two weeks:
pleskbinmailserver--set-outgoing-messages-report-period P2W
To make Plesk send notifications to administrator on outgoing mail every 6 hours:
pleskbinmailserver--set-outgoing-messages-notification-period PT6H
If you use Postfix, you can set outgoing mail mode, which means IP addresses that Plesk uses to send mail from. By default, mail from each domain is sent using the domain’s IP address (the value).
If domain IP addresses are used to send mail, you can make Plesk use the domain names in SMTP greeting, by using the value.
If you need Plesk to send all mail from one IP address, use and corresponding options and
To make Plesk use domain names in SMTP greetings:
pleskbinmailserver--set-outgoing-email-mode domain-name
To make Plesk send all mail from the IP address 10.0.0.1:
pleskbinmailserver--set-outgoing-email-mode explicit-ip -explicit-ipv4 10.0.0.1
To secure the mail server with the SSL/TLS certificate cert3 that is stored at the repository of the domain example.net:
#pleskbinmailserver--set-certificate "cert3" -certificate-repository example.net
Specifies the domain of the SSL/TLS certificate repository. By default, the server repository is used.
This option is used with the command .
To view the help on the use of the utility:
pleskbinmailserver--help
or
Cisco Identity Services Engine Administrator Guide, Release 2.4
Guest and Sponsor Accounts
Guest Accounts—Guests typically represent authorized visitors, contractors, customers, or other users who require temporary access to your network. You can also use guest accounts for employees if you prefer to use one of the guest deployment scenarios to allow employees to access the network. You can access the Sponsor portal to view guest accounts created by a sponsor and by self-registering guests.
Sponsor Accounts—Use the Sponsor portal to create temporary accounts for authorized visitors to securely access your corporate network or the Internet. After creating the guest accounts, you also can use the Sponsor portal to manage these accounts and provide account details to the guests.
Guest accounts can be created by:
Sponsors—On the Admin portal, you can define the access privileges and feature support for sponsors, who can access the Sponsor portal to create and manage guest accounts.
Guests—Guests can also create their own accounts by registering themselves on the Self-Registered Guest portal. Based on the portal configuration, these self-registering guests may need sponsor approval before they receive their login credentials.
Guests can also choose to access the network using the Hotspot Guest portal, which does not require the creation of guest accounts and login credentials, such as username and password.
Employees—Employees who are included in identity stores (such as Active Directory, LDAP, Internal Users) can also gain access through the credentialed Guest portals (Sponsored-Guest and Self-Registered Guest portals), if configured.
After their guest accounts are created, guests can use the Sponsored-Guest portal to log in and gain access to the network.
Guest Types and User Identity Groups
Each guest account must be associated with a guest type. Guest types allow a sponsor to assign different levels of access and different network connection times to a guest account. These guest types are associated with particular network access policies. Cisco ISE includes these default guest types:
Contractor—Users who need access to the network for an extended amount of time, up to a year.
Daily—Guests who need access to the resources on the network for just 1 to 5 days.
Weekly—Users who need access to the network for a couple of weeks.
When creating guest accounts, certain sponsor groups can be restricted to using specific guest types. Members of such a group can create guests with only the features specified for their guest type. For instance, the sponsor group, ALL_ACCOUNTS, can be set up to use only the Contractor guest type, and the sponsor groups, OWN_ACCOUNTS and GROUP_ACCOUNTS, can be set up to use Daily and Weekly guest types. Also, since self-registering guests using the Self-Registered Guest portal typically need access for just a day, you can assign them the Daily guest type.
The guest type defines the user identity group for a guest.
For more information, see:
See the User Identity Groups section in Cisco ISE Admin Guide: Asset Visibility
See the Create a User Identity Group section in Cisco ISE Admin Guide: Asset Visibility
Create or Edit a Guest Type
Besides creating new guest types, you can edit the default Guest Types' default access privileges and settings. The changes that you make are applied to the existing Guest accounts that were created using this Guest Type. Guest users who are logged in will not see these changes until they log out and log in again. You can also duplicate a Guest Type to create additional Guest Types with the same access privileges.
For an existing guest account, attributes are configured for that account by the Guest Type.
If you make changes to a Guest Type, active Guest accounts will take on all the attributes of the updated Guest Type, including the default access times, dates, and duration, which can then be edited. In addition, the custom fields from the original Guest Type are copied to the updated Guest Type.
Each Guest Type has a name, description, and a list of sponsor groups that can create guest accounts with this guest type. You can designate some guest types as follows: use just for self-registering guests, or do not use to create Guest accounts (by any sponsor group).
Procedure
Fill in the following fields.
|
What to do next
Create or modify sponsor groups to use this guest type. For more information, see Sponsor Groups.
If appropriate, assign this guest type to self-registering guests in the Self-Registered Guest portal. For more information, see Create a Self-Registered Guest Portal.
Disable a Guest Type
You cannot delete the last remaining guest type or guest types that are being used by guest accounts. If you want to delete a guest type that is in use, first ensure that it is no longer available for use. Disabling a guest type does not affect guest accounts that were created with that guest type.
The following steps explain how to prepare for and disable a target guest type.
Procedure
| Step 1 | Identify the sponsor groups that allow the sponsor to create guests using the target guest type. Choose Work Centers > Guest Access > Portals and Components > Sponsor Groups, and open each sponsor group and examine the This sponsor group can create accounts using these guest types list. |
| Step 2 | Identify the Self-Registered portals that assign the target guest type. Choose Work Centers > Guest Access > Portals and Components > Guest Portals. Open each Self-Registered Guest portal. If the portal is using the specific guest type, expand Portal Settings, and change the assigned guest type in the field Employees using this portal as guests inherit login options from:. |
| Step 3 | Open the guest type you wish to delete, and delete all sponsor groups that you identified in the previous steps. This action effectively prevents all sponsors from using creating a new guest account with this guest type. Choose Work Centers > Guest Access > Portals and Components > Guest Type. |
That's it. You can't actually delete the guest type. Make sure you don't use in any portals in the future.
Configure Maximum Simultaneous Logins for Endpoint Users
You can configure the maximum number of simultaneous logins that are allowed for a guest.
When the user logs in to a guest portal, and is successfully authenticated, that user's number of existing logins is checked to see if the user has already reached the maximum number of logins. If so, the Guest user is redirected to an error page. An error page is displayed, and the session is stopped. If that user tries to access the internet again, the user's connection is redirected to the guest portal's login page.
Before you begin
Make sure that the authorization profile that you are using in the authorization policy for this portal has Access Type set to . If Access Type is set to , then maximum simultaneous logins is not enforced.
Procedure
| Step 1 |
|
What’s New in the Easy SMTP Server 2.4 serial key or number?
Screen Shot
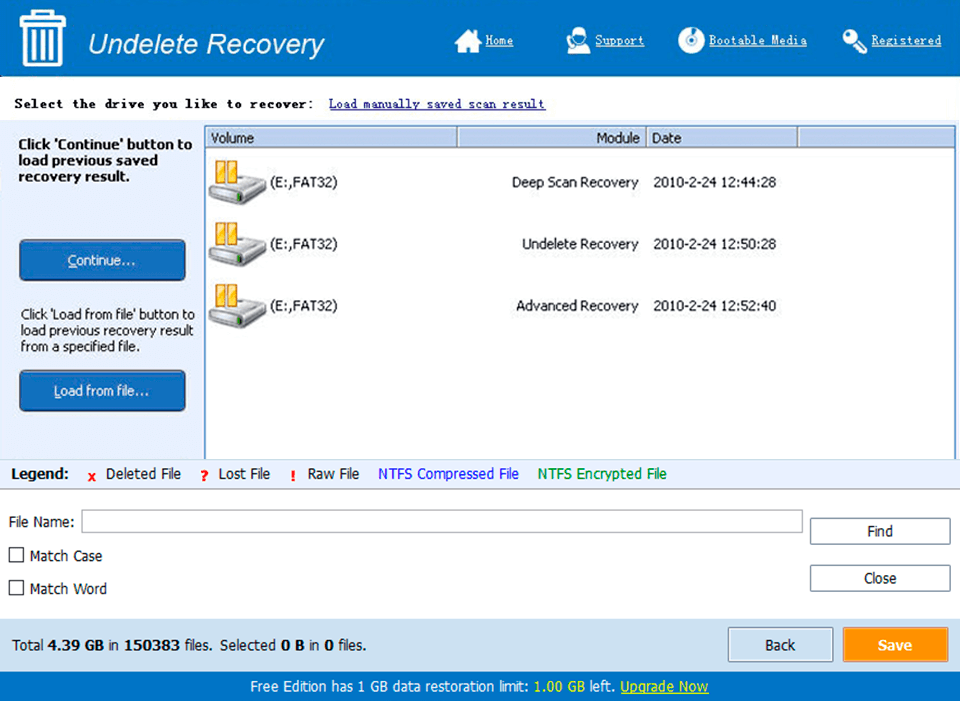
System Requirements for Easy SMTP Server 2.4 serial key or number
- First, download the Easy SMTP Server 2.4 serial key or number
-
You can download its setup from given links:


