
Email Address Juggler 2.4 serial key or number

Email Address Juggler 2.4 serial key or number
6857640 Software Serial Key
3DMark 2000 :Steve Hsu :SG2FE-BDBMN-TL7VC 3DMark 2001 :Steve Hsu :9US0Y-B6H47-C4DYX-FZRKN 3D Studio 3.0 Max :110-19990726 CDKey:SWP9UV vX: 4c2cacb4 Absolute Security v1.00 :SiLicon Surfer [PC] :VQDGKQKWQPMKYQR ACD See 32 2.42 :Steve Hsu :4059021893 Acd See 3.1 :132728175249781441 ACAD 2000 :117-11111111 5X8NUG Add/Remove 4Good 2.0 :Blackstar TRPS98 Code: 6582-2APUZYJHD Add/Remove Cleaner 2.3 :Kwai_Lo [tNO 98] :K17204KE Address Database Pro 4.02 :AEKDB-7895 Adobe Acrobat 4.0 :WCW100R3101909-171 Adobe AfterEffect 4.0 :EWW400R3000406-412 Adobe FramMaker 5.11 :00-0-01-01-5-00D4-D62C70 Adobe PageMill 3.0 :MLJ300R7102421-311 Adobe Photoshop 5.5 :PWW400R7106337-339 Adobe Permiera 5.1 :MBF420U3000205-940 Adobe Type Manager 4.1 :AWW400P0101591-292 Adobe Illustrator 9.0 :ABW900R71111141-999-830 Advance Disk Catalog 1.20b :1303196920041974ERqdY0pQKLeKcBeo Advanced Dialer 1.1 :Steve Hsu :5D672300 Agent 1.8 32.548 :Steve Hsu :HH2W7UY3-131P76L9-MNZARWHC-93XZMZ1RTN856AWT Alarm Master :atlas44 AllAboard 2.2 :SteveHs :TQ7%-C2N3-NXT8-NZBE ALMANAC 3.5c for 95 :TwinHead [TWH/UCF] :A9261579 AMF Daily Planner & PIM 6.1a :AMF6PIMREG96 Amnimated Screen 2.21 :AKAZUKIN :3392C400 AMF Multimedia Jukebox 2.0 :MMJBOXAF Anawave Gravity 2.0b2 :replace _analib.dll 74 09 85 with EB 04 85 AniMagic v1.00b :Steve Hsu com:abc :173E7D79 AntiHack 2.0 :Steve Hsu :81d-9adf-800000 Any Speed 1.3 :JIE LIN :A4482300 AnyFolder Shell Extension :Steve Hsu :1403017 ArGoSoft MX Mailer v1.0 :lxpc97 :293167522363 ArjShell32 :Phrozen Crew '96 :289972970 Astound 4.0 :3260952387 AstroWorld 98 v3.02 :Norway :614-06310200127EAP -(Feb 14
AtGuard v3.1 :NS-100-000-733 Key:FFCD-9766 Audio Compositor 1.3 :jake cwc :2fJS29W2 Audio Grabber 1.62 :51B38A14F6 AuthorWare 5.0 :AW500-06238-47009-90430 Auto Cad Lite 3.0 :160-10264403 Auto Care Center 97 v1.1 :71362180 AutoMate v3.8a :3789406800 AutoShutDown v2.4 :kim (c) tNO :AS3E-TNO-017-DF26
Authentex Datasafe 1.22 :romeo company:D4C :3796792 AutoCad r14 :117-99703105 cd-key:W36H Auto shutdown 3.10 :BERSERKA :AS3E-BSA-186-500A Auto Start 1.5 :Steve Hsu :18571701 Axialis AX-Icons 4.0 :Register :R83WXU-1Q78-LNBB AZPR 2.44 :00003112193920061941gSJqgyJc5a4sCTj4 BarClock :TSWUJ-BPUVG Becky 2.00.05 :Steve Hsu :1809-3437-D348 :stevehsu@bigpond.net.au Best Copy 6.06.1 :Viking :BC-E9F1-9FVE-RLG1-EMSK BlackBoard En/Decoder 1.0 :jake cwc :668 BlackBoard Encrypt Interface :jake cwc :668 BlackBoard PicVu 2.0 :jake cwc :668 BlackICE Defender 2.1 cl :346258C-RS-C473F Black Widow 3.22 :lxcore97 :829-4132/58-16713 Blanch 1.8 :tommy :102c7b2 BlindRead 3.021 :DEYQ-ZV18-1Q2N-DIFJ BoundsChecker V5.0 :Richardcrack :0kadr1rk Bryce 4.0 :BF00WBB-0000000-CUY4:44 PM 8/7/02 Buzof 1.42 :00065536 - 00010133 ByteCatcher Pro V3.0a :239856538576 Cake walk Pro Audio 9 :cwpa900000000 CALIGARI TRUESPACE V4 :6400051000000 Calypso 2.30 :3M9B79VKVK5L7N6SYUB9 CamShot 1.1 :ABC :14058-17335 Canvas 5 Updater :W000-754710 Capture Professional v3.x :SJMISBESTHACKER :TAIWAN :C6-C23-456-AFC CaSeLinr 5.6 :CiB :r8aq6GcQLn CDDA 3.6 :CZY :EZCDDAX3-E0F35BC1-C9EA2E08-261 CdrLabel 4.1 :line1:516619769 line2:876408395 -(Feb 14
CD Wizzard 98 :CW375H2682477176 CGI*StarDuo95 1.03 :AA3852-AA912-45AAA-12345-7896385 Chameleon V5.0 :34059131041712S3 key:A224 Chick It 5.1 :DH-200004 Check Mail v1.02 :Gordon Liu : 5582-9144-35 CleanUp Win95 :+ALI-BABA :688399719833 Clean sweep 3.0 :CSWU3000072702 ClipMate 5.1.4 :Steve Hsu :G013488608048 ClockMan 95 v1.0.057 :Steve Hsu s/n:1203009890 # Users:1 L:597451 ClockTick v2.1.4 :Steve Hsu :1402516080 CloneCd 1.0.2.4 :Crack Man E:crackman@taiwan.tw C:7FBD-C223-4FB4-8AA1 CloneMaster v2.19 :Underworld^SNT :678358010 Closer 1.5 :ibm :422013844604 CMed 2.1b :Crack da WareZ :BMBKEJANEJ Corel 5.0 :CD5-111-123456 Corel Draw 9.0C :dr88r-14z1854048
Com 4.1 :Cracked :376665-193920 Comic-Soft 2.0 :pc97 :042566726433 CommandLine 96 :753868 CommSuite 95 :7000-7166-2080 CompuPic32 4.00 build 950 :CHENZY :888888 code:H882XX9BSG Cookie Pal 1.0.2 :Hackerjack! :3388964 Cool 3D 3.0 :11105-03000-00039406 Cool Edit 2000 :MFD Corp. :Q17EXF5U Cool Info 99 2.7 :Niceshop :CSI481299146736769837279803 Cool Wave Editor 1.52 :tHATDUDE! :VLLTICVT Copernic 99 Plus v3.0 :056-059999999 Coreldraw v7.0 :123456789 Cpu Cool 3.0 :23431708 Create-a-Theme 98 v3.0 :p:58A56V69 c:8246-9729-22 CrossWords U Create 2.0 :two waffles Crystal Ftp v1.0 Preview 2 :qua8SIXh :111701233100000000000000000000 Dana :tHATDUDE! :0912-2349-A818 DataFit v4.1.19 :lxpc97 2d:2766988 3d:7503066 Date 4.20 :5884074 DAO 2.4A 32bit :LordByte in 1996 Company/mail : Phrozen Crew 3191487656Feb 14
Delphi 4.0 :000-000-0000 :A code: 802-5f0 Delrina CommSuite 95 :7020-2175-6499 Delrina Cyberjack 7.0 :7000-7166-2080 Depleter 2.2 :Registered User :85971 DesignCAD 3D v8.0 :6504 0024 1945 DesignExpress Labels :Registered User :QYOBYTK Desktop Deluxe 1.0 :Phrozen Crew :7050 Desktop Themes v1.85 :draXXter :2107358982 Dial Up Magic 1.3 :Registered :1045930556 DirectNet 1.2+ :Steve Hsu :19772-175382-2727-1324 DiskFactory32 2.10 :TeRaPhY :132195911 DiscJuggler 1.05.393 :CDJ-039934FD-FU Disney Screen Saver :DSW-91929-1488 Disappear 98 :110396 Dream Weaver 3.0 :DWW300-08610-27280-95766 Drive Image 3.0 :DP300ENWSCD-101002 Dr.Eye 2001 :DREYE2001-DJYGF-F8Y7L-HIGBBIE-5681 Dr.Salomon's antivirus v6.71 :DTK3H-063095 Drag And File Gold 3.54 :1234567890 Drag And View 4.0 Beta 4a :50000000000000 Drag And Zip :3000000000 Dreamweaver 4.0 :DWW400-03771-57289-73501 DocMan 2.4 :KNJRUT or IUIOOP or AHPUQW or IFNRUX Doghouse 1.2 :Me :JDHUD Dogs of War v2.0 :SteveHsu L:DWSTEVEHSU P:EQNNHLCFBK
Dogz :8000-1830-9488 Double Dynamite 4.3 :884916 Drive Image Pro 2 :DM200JPPCD-874253 Dustman 2.00.103 :Registered :1231E55668 Download Bult 1.6 :lupin :623463B6 special:000111222 DreamWeaver 2.0 :DWW200-09785-18274-81630 Easy Cd Creator 4.0 :110010629931 Easy CD-DA Extractor 3.05 :starless :EZCDDAX3-FC666769-8C425768-446 Easy Pool 3.0 :Steve Hsu :92663 EcoPad v3.3.1 :ED!SON '96 [Xf/UCf] :Dynasty :2302012561 -(Feb 14
EditPlus TextEditor 1.1 : Chafe : 8B868A3D-DB0DF074 EdTex 2.38 :055022239 Elbow Grease 2.0 :LB098765AMF Essocode 7.8 :IQHRIP or :ASZLOTPM Emi-Clock 4.27 :Motosoft :DEB6I9ON6B EmEditor 3.0 :1412-1033-1047-8855 Encore 4.0 :EV40-0-02034-4386 Enhanced Cu-See Me 4.1 :SCBE-001Y-0J8R-SWCT NTS EnterNet 500 1.41 :trackgroove27 ESS Code 7.8 :ASZLOTPM Et2000 v5.1 for Win95 :62256346 Eudora Pro 4.0 :4557201 Extreme Slots 95 1.2 :196458 Extreme 3d :45110-0037-0012-60272 EyeCandy 3.0 :IIIGEBFHMJNB Easy CD Creator 5.0 Platinium:Y-73YHY-SENW9-Y9B4T EZ-Split 2.0 :ES200000001400030340159 EZ-Unzipper 2.55 :all :XPR-667 FAR 1.62 :Niceshop :47AC00 Feurio! V1.60 :Feurio C:Feurio S:11361767 L:3559-1298-9169-8465-6294 Flash 4.0 :FLW400-16664-27865-12345 Flash Get 0.95 :Steve Hsu :09945NE9T2 FlexED32 Ver2.0 :jake cwc :976260262287 FileEx 2.00h :PC97 :655552 File Kick 2.5b :lupin :429-4920266 File Locker 2.3 :73002-50134 File Maker Pro User 2.1 :7001498488 or :7000843902 File Split 2.2 :Niceshop Serial: 313-37-19492 FileName Juggler 1.10 :Name:TKC/PC '97 S/N:12345 P/W:643C-256A-ADFA FileSync v1.4 :Steve Hsu :27579276 File Wiz 1.1 :28013 Fine Print 2000 :Steve Hsu :FRB3-AVV7-LYDX
Fine Print v2.03 for WinNT :RudeBoy [PC] :9477-624597 Firehand Ember 3.1.2 :CLEMENCE CORRIVAU :004-541-64217 FireWorks 4.0 :FWW400-02666-67248-02548 FLameMask 2.6 :Steve Hsu :00000000 Flash 4 :FLW400-16664-27865-12345 Flash 5 :FLW500-13547-37838-54321 -(Feb 14
FlexEd32 v2.0b :Cracked :769806196900 FM StepUp '96 4.02 :Registered User :1997 :3407480960 Folder Guard 4.11 :Niceshop :12345 :F7190020WARP Font Control 1.23 :Steve Hsu :22440. Font Man :Steve Hsu : FCD 51120 FontMonster 3.5 :Steve Hsu :11483. FOX PRO3.0B :111-111111111 FLMASK :SteveHsu :00000000 Fracal Design Painter 4.0 :PW300RAZ0002607-EANY-001 FrameMaker 5.5.6 :20-0-01-01-5-0D2F9-36EC16 Free Cell Plus 1.1b :Steve Hsu :178488 FreeMem Pro 4.2 :296094047829 or :622034946211 Freetel 1.0 :1292-0039-0768-5802 Freehand 9.0 :FHW900-00010-47278-88947 FrontPage 2000 :GC6J3-GTQ62-FP876-94FBR-D3DX8 Fractal Poser 1.03 :FW100RAZ0002042-NTHV-001 Fractal Design Dabbler 2.04 :DW200RAZ0005245-RTJQ-001 Fractal RayDream Studio 4.1 :SW-410-1-2847-62287 FTP 2000 :Steve Hsu :IKELSTC:EM FTP EXPRESS V 1.00.012 :+JUANDA :500131 FTP-Max v1.1 :BLiTZ / [PC97] :NGVJGJ6XSAY4EJ FTP Serv-U 2.2 :serv-u.ini [Galobal][JRegistrationKey=r8fZajeU3JY,ED!SON '96 FTP Voyager v4.0.4.1 :Super XE e:kss@ms1.hinet.net :000008fc FTPSync 2.06 :DESYNC DOMiNATiON :298540400 Ftp Wolf 1.03 :jeagon :FW1-681113 FullDisk v4.3 :DiABLO ORiON :4464BEBC Game Master 7.3 :GM73-033240-067838 Game of Stars 2.5 :WV9NBSGY Gator Edit 1.2 :tHATDUDE! :66666666 Key: 133343023 Gear Replicator 1.2 :9702711341145229 GetRight 4.3 :941829970387 or :268554735020 GetRight 4.5 Beta1 :324556123934 Gif Animator v1.1 :FirstName: Killer+Bee LastName: Phrozen Crew'97 :507549 GIF CONSTRUCTION :Steve Hsu :YVLBB
Gif Movie Gear 2.62 :czy User:MVG29992496 Site:MVG2s9992496 -(Feb 14
12/18/06 Gin Rummy 4.2 :razzia [pc97] :527-633-627 GLDirect 1.01 :Steve Hsu :62EC-A054-215B-1E Global TimeKeeper 1.6 :Steve Hsu :g(?1JrW%)M Go!Zilla v3.5 :stevehsu@tw :X4FWWI21EU Goldmine 95 :11428171950 GoldWave 3.22 :JAKE LN:CWC R:QMKGJV Grabber 1.2.29 :Hacker Club (TW) :083240184386 Graphic Workshop 95 :Steve Hsu :32507 Gravity 1.1 :Jestrz/Phrozen Crew '97 :6172848 :44R8494-4564-242247 Grouper v2.0 :gr1dv Ground Control v1.01 :Nop [Phrozen Crew] :8032-8626-694 GWD Text Editor 1.2 :GTExx/xxx-xxx HardCopy Pro 1.4 :tHE EGOiSTE :ruPR7FzkOs Hard Disk Led 1.1 :11599278 Hard Disk Sleeper 1.42 :Steve Hsu :00143184 Help Pad v1.8 :Steve Hsu :898D1C8F Help Scribble v2.10 :Hank Wang :HScr-987654EC7581E8FB Help Writer's Assistant :Steve Hsu :7319 Hex Work Shop 2.54 :MK121212 Hit-N-Run v1.0 :21664 Holiday Lights 5.0 :Shaligar^Lash :223412341650 HomeSite 4.0 :Steve Hsu :HS40E-727612 Horizon Web Text Ver1.06 :jake cwc :00E026B9 Hot Chili 2.5 :pank :1765-7654-8765 H
Digital Anarchy Beauty Box Video Serial Number
Digital Anarchy Beauty Box Video Serial Number
digital anarchy beauty box serial number, digital anarchy beauty box video serial number
Digital Anarchy Beauty Box Video 2020 Mac is simple and automatic to use. This video plugin automatically identifies skin tones and creates a mask that limits.... Digital Anarchy Beauty Box ... Beauty Box Video skin retouching plugin acts as digital makeup in post-production by incorporating ... Serial Number44C2BEC9F0A8647922EB7D7C-F2A0.. Digital Anarchy Beauty Box Video 4.1 (Win-Mac) Full Version Warez . ... WIN-MAC + serial key YouTube 1280 720 - 126k - jpg toolfarm.com.... Digital Anarchy Beauty Box Video 3.0.3 AE Adobe ... Enter Beauty Box serial number, .... 7b042e0984 Digital Anarchy Beauty Box Video 4.1 (Win/Mac) ... Download digital anarchy flickerfree mac serial number generator, crack or.... Digital Anarchy Beauty Box Video 4 Crack is best automatic masking and skin retouching capabilities of any plugin. Beauty Box Video Full.... digital anarchy beauty box 3.0.7 for photoshop digital anarchy beauty box video serial number. Download,,now,,the,,serial,,number,,for,,Digital,,Beauty.,,All,.... The Beauty Box Video skin retouching plugin acts as digital makeup in post-production by .... So the regular serial number will now work without any problems.. Beauty Box Video After EffectsPremiere ProFinal Cut Pro X .... Overview of beauty box video skin retouching plugin. This app will remove the current version of your digital anarchy product it will not remove the serial number information.. In this topic, we share Digital Anarchy Beauty Box Video 4.2.3 (Windows) and 4.1.0 (MacOS) Full Crack with Serial number for After Effects and.... Digital Anarchy Beauty Box Video 4.2.3 for After Effects & Premiere Pro. Th By, 01/09/2018 | 3:46 GMT+7 After Effect, Phn mm, Premiere Pro 6.771 views.. RA Beauty Retouch Panel 3.3 with Pixel Juggler for Adobe Photoshop WIN-MAC cracked (FULL),Ultimate Retouch Panel 3.7.73 for Adobe Photoshop Cracked.... Jim Tierney and Digital Anarchy have produced 'Beauty Box' for both Final ... Looking to get back into the video genre, Jim Tierney and Digital Anarchy ... One serial number is all I needed for both the Final Cut Pro and Adobe.... I've lost the plug-in email with my serial numbers and I need to reinstall. ... Older versions of existing products, like Beauty Box Video 1.0, are available on the.... For more information, please email sales@digitalanarchy.com. ... When you apply Beauty Box to footage, FCP renders the plugin and caches the ... When you enter the serial number, FCP doesn't recognize that any .... how fast your hardware is, which video editing application you're using and ... 2019 Digital Anarchy.
Der Software-Entwickler Digital Anarchy hat ein Update zu ihrer Beauty Box herausgebracht. Mit Beauty Box Video 4.0 knnen.... Buy DIGITAL ANARCHY Beauty Box Video 4.0 For After Effects & Premiere Pro Single User New (BEAUTYVID-AE) with fast shipping and top-rated customer.... ... mac, Digital Anarchy Beauty Box v2 portable, Digital Anarchy Beauty Box v2 serial number. ... Digital .... Both Flicker Free and Beauty Box Video have been updated for the ... So the regular serial number will now work without any problems.
0bde44ddc2
dirac live room correction suite cracked
hipertexto santillana fisica 1 solucionario pdf
forced human toilet stories
Koi Mere Dil Se Poochhe full movie in hindi hd 720p
Swarg full movie in hindi hd 720p
59 secret scripts pdf 294
Xbox 360 Emulator BIOS v3.2.4.rar 51.73 KB
kinobody greek god pdf 290
ra one hd movie full download
download 720p Rab Ne Bana Di Jodi movies in hindi
Versions: 00010203040506RFC 8236
Network Working Group F. Hao, Ed. Internet-Draft Newcastle University (UK) Intended status: Informational January 26, 2016 Expires: July 29, 2016 J-PAKE: Password Authenticated Key Exchange by Jugglingdraft-hao-jpake-02 Abstract This document specifies a Password Authenticated Key Exchange by Juggling (J-PAKE) protocol. This protocol allows the establishment of a secure end-to-end communication channel between two remote parties over an insecure network solely based on a shared password, without requiring a Public Key Infrastructure (PKI) or any trusted third party. Status of This Memo This Internet-Draft is submitted in full conformance with the provisions of BCP 78 and BCP 79. Internet-Drafts are working documents of the Internet Engineering Task Force (IETF). Note that other groups may also distribute working documents as Internet-Drafts. The list of current Internet- Drafts is at http://datatracker.ietf.org/drafts/current/. Internet-Drafts are draft documents valid for a maximum of six months and may be updated, replaced, or obsoleted by other documents at any time. It is inappropriate to use Internet-Drafts as reference material or to cite them other than as "work in progress." This Internet-Draft will expire on July 29, 2016. Copyright Notice Copyright (c) 2016 IETF Trust and the persons identified as the document authors. All rights reserved. This document is subject to BCP 78 and the IETF Trust's Legal Provisions Relating to IETF Documents (http://trustee.ietf.org/license-info) in effect on the date of publication of this document. Please review these documents carefully, as they describe your rights and restrictions with respect to this document. Code Components extracted from this document must include Simplified BSD License text as described in Section 4.e of Hao Expires July 29, 2016 [Page 1]
Internet-Draft J-PAKE January 2016 the Trust Legal Provisions and are provided without warranty as described in the Simplified BSD License. Table of Contents 1. Introduction . . . . . . . . . . . . . . . . . . . . . . . . 21.1. Requirements language . . . . . . . . . . . . . . . . . . 31.2. Notations . . . . . . . . . . . . . . . . . . . . . . . . 32. J-PAKE Protocol . . . . . . . . . . . . . . . . . . . . . . . 42.1. Protocol setup . . . . . . . . . . . . . . . . . . . . . 42.2. Two-round key exchange . . . . . . . . . . . . . . . . . 42.3. Three-pass variant . . . . . . . . . . . . . . . . . . . 62.4. Key confirmation . . . . . . . . . . . . . . . . . . . . 62.5. Computational cost . . . . . . . . . . . . . . . . . . . 73. Security Considerations . . . . . . . . . . . . . . . . . . . 84. IANA Considerations . . . . . . . . . . . . . . . . . . . . . 95. Acknowledgements . . . . . . . . . . . . . . . . . . . . . . 96. References . . . . . . . . . . . . . . . . . . . . . . . . . 96.1. Normative References . . . . . . . . . . . . . . . . . . 96.2. Informative References . . . . . . . . . . . . . . . . . 10 Author's Address . . . . . . . . . . . . . . . . . . . . . . . . 111. Introduction Password-Authenticated Key Exchange (PAKE) is a technique that aims to establish secure communication between two remote parties solely based on their shared password, without relying on a Public Key Infrastructure or any trusted third party [BM92]. The first PAKE protocol, called EKE, was proposed by Steven Bellovin and Michael Merrit in 1992 [BM92]. Other well-known PAKE protocols include SPEKE (by David Jablon in 1996) [Jab96] and SRP (by Tom Wu in 1998) [Wu98]. SRP has been revised several times to address reported security and efficiency issues. In particular, the version 6 of SRP, commonly known as SRP-6, is specified in [RFC5054]. This document specifies a PAKE protocol called Password Authenticated Key Exchange by Juggling (J-PAKE), which was designed by Feng Hao and Peter Ryan in 2008 [HR08]. There are a few factors that may be considered in favor of J-PAKE over others. First, J-PAKE has security proofs, while equivalent proofs are lacking in EKE, SPEKE and SRP-6. Second, J-PAKE is not patented. It follows a completely different design approach from all other PAKE protocols, and is built upon a well-established Zero Knowledge Proof (ZKP) primitive: Schnorr NIZK proof [I-D-Schnorr]. Third, J-PAKE is efficient. It adopts novel engineering techniques to optimize the use of ZKP so that overall the protocol is sufficiently efficient for practical use. Fourth, J-PAKE is designed Hao Expires July 29, 2016 [Page 2]
Internet-Draft J-PAKE January 2016 to work generically in both the finite field and elliptic curve setting (i.e., DSA and ECDSA-like groups). Unlike SPEKE, it does not require any extra primitive to hash passwords onto a designated elliptic curve. Finally, J-PAKE has been used in real-world applications at a relatively large scale, e.g., Firefox sync, Pale moon browser and Google Nest products; has been included into widely distributed open source libraries such as OpenSSL, Network Security Services (NSS) and the Bouncy Castle; since 2015, has been included into Thread as a standard key agreement mechanism for IoT (Internet of Things) applications; and currently is being standardized by ISO/ IEC 11770-4. 1.1. Requirements language The key words "MUST", "MUST NOT", "REQUIRED", "SHALL", "SHALL NOT", "SHOULD", "SHOULD NOT", "RECOMMENDED", "MAY", and "OPTIONAL" in this document are to be interpreted as described in RFC 2119 [RFC2119]. 1.2. Notations The following notations are used in this document: o Alice: the assumed identity of the first party in the protocol o Bob: the assumed identity of the second party in the protocol o s: a low-entropy secret shared between Alice and Bob o p: a large prime o q: a large prime divisor of p-1 o Zp*: a multiplicative group of integers modulo p o Gq: a subgroup of Zp* with primer order q o g: a generator of Gq o g^x: g raised to the power of x o a mod b: a modulo b o a * b: a multiplied by b o a || b: concatenation of a and b o H: a secure one-way hash function Hao Expires July 29, 2016 [Page 3]
Internet-Draft J-PAKE January 2016 o KDF(a): Key Derivation Function with input a o HMAC(MacKey, MacData): HMAC function with MacKey as the key and MacData as the input data 2. J-PAKE Protocol2.1. Protocol setup The J-PAKE protocol uses exactly the same group setting as DSA (or ECDSA). For simplicity, this document will only describe the J-PAKE protocol in the DSA-like group setting. The protocol works basically the same in the ECDSA-like group setting, except that the underlying multiplicative group over a finite field is replaced by an additive group over an elliptic curve. Let Gq denote a subgroup of Zp* with prime order q, in which the Decisional Diffie-Hellman problem (DDH) is intractable. The p and q are large primes and q divides p-1. Let g be a generator in Gq. Any non-identity element in Gq can be a generator. The two communicating parties, Alice and Bob, both agree on (p, q, g). Values of (p, q, g), as defined by NIST, can be found in the appendix of [I-D-Schnorr]. [[Q1:: The reference is an accompanying internet draft submission to IETF and it needs to be updated once it is accepted by IETF. --Hao]] Let s be the shared secret between Alice and Bob. The secret may be a password, a hash of the password or any other derivative from a password. This does not make any difference to the protocol. The only assumptions are that s has low-entropy and that the value of s falls within [1, q-1]. (Note that s must not be 0 for any non-empty secret.) 2.2. Two-round key exchange Round 1: Alice selects x1 uniformly at random from [0, q-1] and x2 from [1, q-1]. Similarly, Bob selects x3 uniformly at random from [0, q-1] and x4 from [1, q-1]. o Alice -> Bob: g^{x1} mod p, g^{x2} mod p and knowledge proofs for x1 and x2 o Bob -> Alice: g^{x3} mod p, g^{x4} mod p and knowledge proofs for x3 and x4 In this round, the sender must demonstrate the knowledge of the ephemeral private keys. A suitable technique is to use the Schnorr NIZK proof [I-D-Schnorr]. As an example, suppose one wishes to prove Hao Expires July 29, 2016 [Page 4]
Internet-Draft J-PAKE January 2016 the knowledge of the exponent for X = g^x mod p. The generated Schnorr NIZK proof will contain: {UserID, V = g^v mod p, r = v - x * h mod q} where UserID is the unique identifier for the prover, v is a number chosen uniformly at random from [0, q-1] and h = H(g || V || X || UserID). The "uniqueness" of UserID is defined from the user's perspective -- for example, if Alice communicates with several parties, she shall associate a unique identity with each party. Upon receiving a Schnorr NIZK proof, Alice shall check the prover's UserID is a valid identity and is different from her own identity. During the key exchange process using J-PAKE, each party shall ensure that the other party has been consistently using the same identity throughout the protocol execution. Details about the Schnorr NIZK proof, including the generation and the verification procedures, can be found in [I-D-Schnorr]. When this round finishes, Alice verifies the received knowledge proofs as specified in [I-D-Schnorr] and also checks that g^{x4} != 1 mod p. Similarly, Bob verifies the received knowledge proofs and also checks that g^{x2} != 1 mod p. Round 2: o Alice -> Bob: A=g^{(x1+x3+x4)*x2*s} mod p and a knowledge proof for (x2*s) o Bob -> Alice: B=g^{(x1+x2+x3)*x4*s} mod p and a knowledge proof for (x4*s) In this round, the Schnorr NIZK proof is computed in the same way as in the previous round except that the generator is different. For Alice, the generator used is g^(x1+x3+x4) instead of g; for Bob, the generator is g^(x1+x2+x3) instead of g. Since any non-identity element in Gq can be used as a generator, Alice and Bob just need to ensure g^(x1+x3+x4) != 1 mod p and g^(x1+x2+x3) != 1 mod p. With overwhelming probability, these inequalities are statistically guaranteed even when the user is communicating with an adversary (i.e., in an active attack). Nonetheless, for absolute guarantee, the receiving party may wish to explicitly check if these inequalities hold, and the cost of doing that is negligible. When the second round finishes, Alice and Bob verify the received knowledge proofs and then compute the key material K as follows: o Alice computes K = (B/g^{x2*x4*s})^{x2} mod p = g^{(x1+x3)*x2*x4*s} mod p o Bob computes K = (A/g^{x2*x4*s})^{x4} mod p = g^{(x1+x3)*x2*x4*s} mod p Hao Expires July 29, 2016 [Page 5]
Internet-Draft J-PAKE January 2016 With the same keying material K, both parties can derive a common session key k using a Key Derivation Function (KDF). If the subsequent secure communication uses a symmetric cipher in an authenticated mode (say AES-GCM), then one key is sufficient, i.e., k = KDF(K). Otherwise, the session key should comprise an encryption key (for confidentiality) and a MAC key (for integrity), i.e., k = k_enc || k_mac, where k_enc = KDF(K || "JPAKE_ENC") and k_mac = KDF(K || "JPAKE_MAC"). The exact choice of the KDF is left to specific applications to define. (In many cases, the KDF can simply be a cryptographic hash function, e.g., SHA-256.) 2.3. Three-pass variant The two-round J-PAKE protocol is completely symmetric, which significantly simplifies the security analysis. In practice, one party normally initiates the communication and the other party responds. In that case, the protocol will be completed in three passes instead of two rounds. The two-round J-PAKE protocol can be trivially changed to three passes without losing security. Assume Alice initiates the key exchange. The three-pass variant works as follows: 1. Alice -> Bob: g^{x1} mod p, g^{x2} mod p, knowledge proofs for x1 and x2. 2. Bob -> Alice: g^{x3} mod p, g^{x4} mod p, B=g^{(x1+x2+x3)*x4*s mod p, knowledge proofs for x3, x4, and x4*s. 3. Alice -> Bob: A=g^{(x1+x3+x4)*x2*s} mod p and a knowledge proof for x2*s. Both parties compute the session keys in exactly the same way as before. 2.4. Key confirmation The two-round J-PAKE protocol (or three-pass variant) provides cryptographic guarantee that only the authenticated party who used the same password at the other end is able to compute the same session key. So far the authentication is only implicit. For achieving explicit authentication, an additional key confirmation procedure should be performed. This is to ensure that both parties have actually obtained the same session key. There are several explicit key confirmation methods available. They are generically applicable to all key exchange protocols, not just J-PAKE. In general, it is recommended to use a different key from Hao Expires July 29, 2016 [Page 6]
Internet-Draft J-PAKE January 2016 the session key for key confirmation, say using k' = KDF(K || "JPAKE_KC"). The advantage of using a different key for key confirmation is that the session key remains indistinguishable from random after the key confirmation process (although this perceived advantage is actually subtle and only theoretical). Two key- confirmation methods are presented here. The first method is based on the one used in the SPEKE protocol [Jab96]. Suppose Alice initiates the key confirmation. Alice sends to Bob H(H(k')), which Bob will verify. If the verification is successful, Bob sends back to Alice H(k'), which Alice will verify. This key confirmation procedure needs to be completed in two rounds, as shown below. 1. Alice -> Bob: H(H(k')) 2. Bob -> Alice: H(k') The second method is based on the unilateral key confirmation scheme specified in NIST SP 800-56A Revision 1 [BJS07]. Alice and Bob send to each other a MAC tag, which they will verify accordingly. This key confirmation procedure can be completed in one round, as shown below. o Alice -> Bob: MacTagAlice = HMAC(k', "KC_1_U || Alice || Bob || g^x1 || g^x2 || g^x3 || g^x4") o Bob -> Alice: MacTagBob = HMAC(k', "KC_1_U || Bob || Alice || g^x3 || g^x4 || g^x1 || g^x2") The second method assumes an additional secure MAC function (HMAC) and is slightly more complex than the first method; however, it can be completed within one round and it preserves the overall symmetry of the protocol implementation. This may prove desirable in some applications. 2.5. Computational cost In J-PAKE, the modular exponentiations are the predominant factors in the computation. Hence, the computational cost is estimated based on counting the number of such modular exponentiations. Note that it takes one exponentiation to generate a Schnorr NIZK proof and two to verify it [I-D-Schnorr]. For Alice, she has to perform 8 exponentiations in the first round, 4 in the second round, and 2 in the final computation of the session key. Hence, that is 14 modular exponentiations in total. Based on the symmetry, the computational cost for Bob is exactly the same. Hao Expires July 29, 2016 [Page 7]
Internet-Draft J-PAKE January 20163. Security Considerations A PAKE protocol is designed to provide two functions in one protocol execution. The first one is to provide zero-knowledge authentication of a password. It is called "zero knowledge" because at the end of the protocol, the two communicating parties will learn nothing more than one bit information: whether the passwords supplied at two ends are equal. Therefore, a PAKE protocol is naturally resistant against phishing attacks. The second function is to provide session key establishment if the two passwords are equal. The session key will be used to protect the confidentiality and integrity of the subsequent communication. More concretely, a secure PAKE protocol shall satisfy the following security requirements [HR10]. 1. Off-line dictionary attack resistance: It does not leak any information that allows a passive/active attacker to perform off- line exhaustive search of the password. 2. Forward secrecy: It produces session keys that remain secure even when the password is later disclosed. 3. Known-key security: It prevents a disclosed session key from affecting the security of other sessions. 4. On-line dictionary attack resistance: It limits an active attacker to test only one password per protocol execution. First, a PAKE protocol must resist off-line dictionary attacks. A password is inherently weak. Typically, it has only about 20-30 bits entropy. This level of security is subject to exhaustive search. Therefore, in the PAKE protocol, the communication must not reveal any data that allows an attacker to learn the password through off- line exhaustive search. Second, a PAKE protocol must provide forward secrecy. The key exchange is authenticated based on a shared password. However, there is no guarantee on the long-term secrecy of the password. A secure PAKE scheme shall protect past session keys even when the password is later disclosed. This property also implies that if an attacker knows the password but only passively observes the key exchange, he cannot learn the session key. Third, a PAKE protocol must provide known key security. A session key lasts throughout the session. An exposed session key must not cause any global impact on the system, affecting the security of other sessions. Hao Expires July 29, 2016 [Page 8]
Internet-Draft J-PAKE January 2016 Finally, a PAKE protocol must resist on-line dictionary attacks. If the attacker is directly engaging in the key exchange, there is no way to prevent such an attacker trying a random guess of the password. However, a secure PAKE scheme should mitigate the effect of the on-line attack to the minimum. In the best case, the attacker can only guess exactly one password per impersonation attempt. Consecutively failed attempts can be easily detected and the subsequent attempts can be thwarted accordingly. It has been proven in [HR10] that J-PAKE satisfies all of the four requirements based on the assumptions that there exists a secure cryptographic hash function and that the Decisional Diffie-Hellman problem is intractable. An independent study that proves security of J-PAKE in a model with algebraic adversaries and random oracles can be found in [ABM15]. By comparison, it has been known that EKE has the problem of leaking partial information about the password to a passive attacker, hence not satisfying the first requirement [Jas96]. For SPEKE and SRP-6, an attacker may be able to test more than one password in one on-line dictionary attack (see [Zha04] and [Hao10]), hence they do not satisfy the fourth requirement in the strict theoretical sense. Furthermore, SPEKE is found vulnerable to an impersonation attack and a key-malleability attack [HS14]. These two attacks affect the SPEKE protocol specified in Jablon's original 1996 paper [Jab96] as well in the latest IEEE P1363.2 standard draft D26 and the latest published ISO/IEC 11770-4:2006 standard. As a result, the specification of SPEKE in ISO/IEC 11770-4 is being revised to address the identified problems. 4. IANA Considerations This document has no actions for IANA. 5. Acknowledgements The editor of this document would like to thank Dylan Clarke and Siamak F. Shahandashti for useful comments. This work was supported by the EPSRC First Grant EP/J011541/1. 6. References6.1. Normative References [RFC2119] Bradner, S., "Key words for use in RFCs to Indicate Requirement Levels", BCP 14, RFC 2119, DOI 10.17487/RFC2119, March 1997, <http://www.rfc-editor.org/info/rfc2119>. Hao Expires July 29, 2016 [Page 9]
Internet-Draft J-PAKE January 2016 [RFC5054] Taylor, D., Wu, T., Mavrogiannopoulos, N., and T. Perrin, "Using the Secure Remote Password (SRP) Protocol for TLS Authentication", RFC 5054, DOI 10.17487/RFC5054, November 2007, <http://www.rfc-editor.org/info/rfc5054>. [ABM15] Abdalla, M., Benhamouda, F., and P. MacKenzie, "Security of the J-PAKE Password-Authenticated Key Exchange Protocol", IEEE Symposium on Security and Privacy, May 2015. [BM92] Bellovin, S. and M. Merrit, "Encrypted Key Exchange: Password-based Protocols Secure against Dictionary Attacks", IEEE Symposium on Security and Privacy, May 1992. [HR08] Hao, F. and P. Ryan, "Password Authenticated Key Exchange by Juggling", 16th Workshop on Security Protocols (SPW'08), May 2008. [HR10] Hao, F. and P. Ryan, "J-PAKE: Authenticated Key Exchange Without PKI", Springer Transactions on Computational Science XI, 2010. [HS14] Hao, F. and S. Shahandashti, "The SPEKE Protocol Revisited", Security Standardisation Research, December 2014. [Jab96] Jablon, D., "Strong Password-Only Authenticated Key Exchange", ACM Computer Communications Review, October 1996. [Wu98] Wu, T., "The Secure Remote Password protocol", Symposimum on Network and Distributed System Security, March 1998. [I-D-Schnorr] Hao, F., "Schnorr NIZK proof: Non-interactive Zero Knowledge Proof for Discrete Logarithm", Internet Draft submitted to IETF, 2013. 6.2. Informative References [BJS07] Barker, E., Johnson, D., and M. Smid, "Recommendation for Pair-Wise Key Establishment Schemes Using Discrete Logarithm Cryptography (Revised)", NIST Special Publication 800-56A, March 2007, <http://csrc.nist.gov/publications/nistpubs/800-56A/SP800-56A_Revision1_Mar08-2007.pdf>. Hao Expires July 29, 2016 [Page 10]
Internet-Draft J-PAKE January 2016 [Jas96] Jaspan, B., "Dual-Workfactor Encrypted Key Exchange: Efficiently Preventing Password Chaining and Dictionary Attacks", USENIX Symphosium on Security, July 1996. [Zha04] Zhang, M., "Analysis of The SPEKE Password-Authenticated Key Exchange Protocol", IEEE Communications Letters, January 2004. [Hao10] Hao, F., "On Small Subgroup Non-Confinement Attacks", IEEE conference on Computer and Information Technology, 2010. Author's Address Feng Hao (editor) Newcastle University (UK) Claremont Tower, School of Computing Science, Newcastle University Newcastle Upon Tyne United Kingdom Phone: +44 (0)192-208-6384 EMail: feng.hao@ncl.ac.uk Hao Expires July 29, 2016 [Page 11]
Html markup produced by rfcmarkup 1.129b, available from https://tools.ietf.org/tools/rfcmarkup/
What’s New in the Email Address Juggler 2.4 serial key or number?
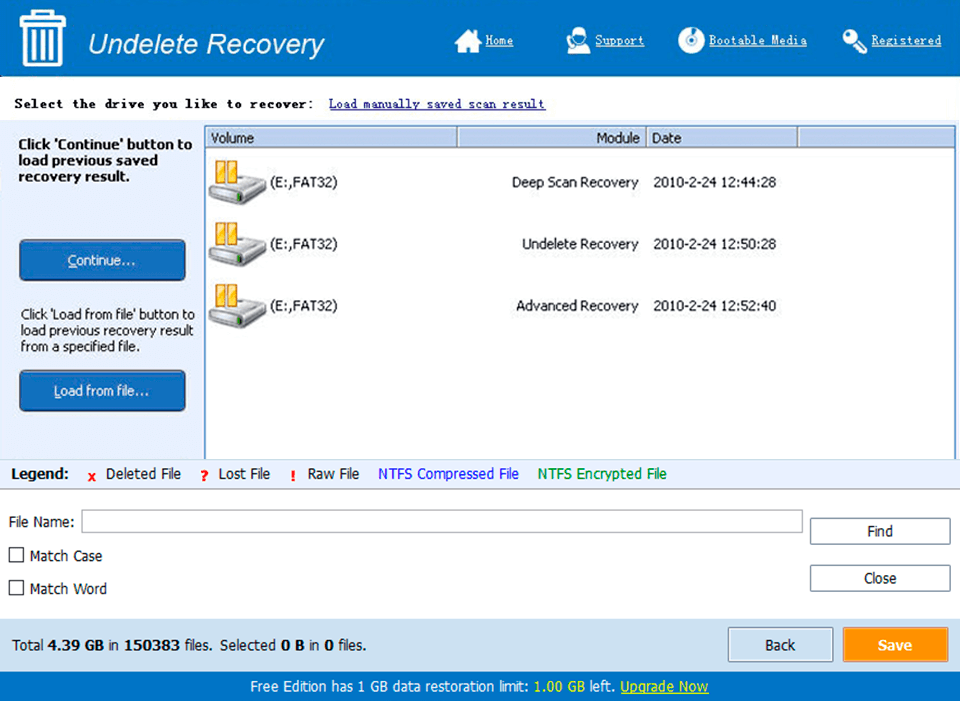
Screen Shot
System Requirements for Email Address Juggler 2.4 serial key or number
- First, download the Email Address Juggler 2.4 serial key or number
-
You can download its setup from given links:


