
HTML To PHP Converter 4.2.1.8 serial key or number

HTML To PHP Converter 4.2.1.8 serial key or number
Thursday, September 30, 2010
Dynamic HTML Editor v5.6.3 Multilingual Incl Keygen-MESMERiZE

Also great for creating server pages (asp, jsp, php, cfm, …)
· Dashes and Caps
· Overlays for graphical objects
· Integrated FTP Client
· Extensions
· New template management
· Transparent and Scrollable Layers
· Date of Modify Object
· Additional Components Window
· New Label editor with RTL support
· Form with integrated email support (with ASP or PHP processor)
V.5.6 (build 02)- Jul 03, 2010
• When the Extension Builder is closed extensions are reloaded automatically
• Added some "Delete" buttons in panels so it is simpler to remove options where possible
• Added the preview of a picture in the Extension Image Gallery panel
• Changed the extension menu
• Fix: some problem related to the PNG32 support with some extensions
• Fix: some problems related to the extension builder have been fixed
• Fix: now it is possible to remove an extension thumbnail in a simple way using the
properties panel
Any DVD Cloner Platinum v1.0.7 Incl KeyMaker-DVT

Zooom v2.4.4 MacOSX Incl. Keymaker-COR

* Move and resize your windows with a flick of the mouse
* Bring windows to the front by moving the mouse over the window
* Use magnetics to align/snap windows to each other – its as easy as 1, 2… done!
* Easy to learn
Release name: Zooom.v2.3.3.MacOSX.Incl.Keymaker-CORE
Size: 5.32 mb
Tuesday, September 28, 2010
Rar Password Unlocker v3.2.0.1 | 5 Mb

If you forget the WinRAR /RAR password, This RAR password recovery software may be your best resort. RAR Password Unlocker is proved to be a helpful tool for users to recover forgotten RAR password. It supports brute-force attack, brute force with mask and dictionary attack..
MP3 Cutter Joiner New in version 3.00:

MP3 Cutter Joiner New in version 3.00:
· Support ID3 editor. You can edit the title, artist, album, genre, year and comment information of your created files.
· Support MP3 VBR and OGG VBR
· Support WMA 9
· Support flash demo
· Support MP3 WAV OGG WMA to MP3 RM OGG WAV WMA.
· Support MP3 Cutter, MP3 Joiner, WMA Cutter, WMA Joiner.
What's benefit after registering:
1. Convert without number limitation !
2. Lifetime free update/upgrade !
3. No annoying reminding Message !
4. Get technology support free !
Saturday, September 18, 2010
USB Safely Remove 4.3.2.950 Final best

USB Safely Remove - is a neat and reliable replacement for the standard 'Safely Remove Hardware' tool with unique feature "Return Device Back!" and an ability to know what prevent a device from being stopped.
The program saves time and extends abilities of active users of hot-plug devices (USB, SATA, FireWire, PCMCIA).
Opportunities it gives for active users of hot-plug devices
It saves time and gets rid of problems...
Displaying what prevent a device from being stopped
Safe removal via hotkeys
Lets you recognize a device in a snap..
The handy menu with device icons
Real device names and ability to rename them
Feature to hide unnecessary to stop devices
Extends your hot-plug opportunities...
Program autorun on device connection\disconnection
Command line for safe removal
Does unique things!
Hiding of "empty" card reader drives
Card reader memory cards ejection one-by-one
Returning just stopped device back!
And much more...
Wifi Hack Ultimate AIO 2010

Wifi Hack Ultimate AIO 2010 | 163 MB
INFO
This time we bring you the best software to hack the WiFi networks 2010. The compilation includes powerful encryption software in network detection and ideal for hacking WiFi networks.Download Programs to hack Free Full WiFi networks.
This AiO contains:
Windows Tools 1
WiresHark
AirSnare
Kismet
aircrack
WirelessKeyView
Wifi Monster
NetStumbler
Easy Wifi Radar
SmartSniff
Ettercap
WinPcap
CommView
Windows Tools 2
Nmap
WiFi Internet Access Blocker
iPig WiFi HotSpot VPN Security
Kismet
Wirelessmon
PocketWarrior
Inssider
RemoteAnyWhere
PmoniPacketMon
ApTools
WiFiFoFum
Advanced Port Scanner
NetSurveyor
Backtrack
Download link for BackTrack 4 Pre Release
Download link for BackTrack 4 Beta Release
Download link for BackTrack 3 VmWare Image
Download link for BackTrack 3
Download link for BackTrack 3 USB Version
PDF?s & Tutorials
Hacking Wireless Networks
Cracking WEP and WPA WiFi
Wifi Hacking
Hacking Asus WL520gU
BackTrack PDFs
O-Reilly Wireless Hacks
FBI Teaches how to break WiFi
WiFi Advanced Fuzzing
Wifi Security
Wireless Sniffing WiresHark
Wireless Hacking Tools
Bonus Software
Net Tools
WepGen
Cantennator
Anchorfree
Cain and Abel
Wifi Drivers
Brutus
VmWare Keygen
LanHelper
Sonne Video Converter 11.3.0.2070

Sonne Video Converter 11.3.0.2070 | 58.7 MB

Sonne Video Converteris a professional video converter that can convert almost all video formats such as convert WMV to MPEG, WMV to AVI, AVI to MPEG, AVI to MP4 Sonne Video Converter supports a wide range of video formats including AVI, MPEG, MPEG 1, MPEG 2, MPEG 4, VCD, DVD, SVCD, RMVB, RM, WMV, MOV, DIVX.
It has extremely fast conversion speed and high quality, which makes you enjoy your video converting. And the user-friendly interface lets you convert video files between many formats with ease.
Sonne Video Converter / Key Function
- Convert WMV to MPEG, WMV to AVI, AVI to MPEG, AVI to MP4....
- Supports a wide range of video formats (AVI, MPEG, MPEG 1, MPEG 2, MPEG 4, VCD, DVD, MPEG, RM, WAV, SWF....)
- Batch convert video formats.
- Split videos into desired size.
- Support any user defined video file formats as the output.
- You can customize video profiles video and parameters for output video.
- Fast conversion speed with high quality.
- User-friendly interface that is easy to use
MAGIX Software Collection Updated 14.09.2010
Magix which has over 15 years of experience could create the best edit and multimedia editor software for you.
Toolkit includes:
Thursday, September 16, 2010
Is Your Nokia Cell Phone Origina
Press the following on your mobile *#06#to see your Phone’s IMEI number(serial number).
Then check the 7th and 8th numbers
Phone serial no. x x x x x x ? ? x x x x x x x
IF the Seventh & Eighth digits of your cell phone are 02 or
Updated by: 6818, 8398, 8399 PROPOSED STANDARD
Errata Exist
Network Working Group D. Cooper Request for Comments: 5280 NIST Obsoletes: 3280, 4325, 4630 S. Santesson Category: Standards Track Microsoft S. Farrell Trinity College Dublin S. Boeyen Entrust R. Housley Vigil Security W. Polk NIST May 2008 Internet X.509 Public Key Infrastructure Certificateand Certificate Revocation List (CRL) Profile Status of This Memo This document specifies an Internet standards track protocol for the Internet community, and requests discussion and suggestions for improvements. Please refer to the current edition of the "Internet Official Protocol Standards" (STD 1) for the standardization state and status of this protocol. Distribution of this memo is unlimited. Abstract This memo profiles the X.509 v3 certificate and X.509 v2 certificate revocation list (CRL) for use in the Internet. An overview of this approach and model is provided as an introduction. The X.509 v3 certificate format is described in detail, with additional information regarding the format and semantics of Internet name forms. Standard certificate extensions are described and two Internet-specific extensions are defined. A set of required certificate extensions is specified. The X.509 v2 CRL format is described in detail along with standard and Internet-specific extensions. An algorithm for X.509 certification path validation is described. An ASN.1 module and examples are provided in the appendices. Cooper, et al. Standards Track [Page 1]
RFC 5280 PKIX Certificate and CRL Profile May 2008 Table of Contents 1. Introduction ....................................................42. Requirements and Assumptions ....................................62.1. Communication and Topology .................................72.2. Acceptability Criteria .....................................72.3. User Expectations ..........................................72.4. Administrator Expectations .................................83. Overview of Approach ............................................83.1. X.509 Version 3 Certificate ................................93.2. Certification Paths and Trust .............................103.3. Revocation ................................................133.4. Operational Protocols .....................................143.5. Management Protocols ......................................144. Certificate and Certificate Extensions Profile .................164.1. Basic Certificate Fields ..................................164.1.1. Certificate Fields .................................174.1.1.1. tbsCertificate ............................184.1.1.2. signatureAlgorithm ........................184.1.1.3. signatureValue ............................184.1.2. TBSCertificate .....................................184.1.2.1. Version ...................................194.1.2.2. Serial Number .............................194.1.2.3. Signature .................................194.1.2.4. Issuer ....................................204.1.2.5. Validity ..................................224.1.2.5.1. UTCTime ........................234.1.2.5.2. GeneralizedTime ................234.1.2.6. Subject ...................................234.1.2.7. Subject Public Key Info ...................254.1.2.8. Unique Identifiers ........................254.1.2.9. Extensions ................................264.2. Certificate Extensions ....................................264.2.1. Standard Extensions ................................274.2.1.1. Authority Key Identifier ..................274.2.1.2. Subject Key Identifier ....................284.2.1.3. Key Usage .................................294.2.1.4. Certificate Policies ......................324.2.1.5. Policy Mappings ...........................354.2.1.6. Subject Alternative Name ..................354.2.1.7. Issuer Alternative Name ...................384.2.1.8. Subject Directory Attributes ..............394.2.1.9. Basic Constraints .........................394.2.1.10. Name Constraints .........................404.2.1.11. Policy Constraints .......................434.2.1.12. Extended Key Usage .......................444.2.1.13. CRL Distribution Points ..................454.2.1.14. Inhibit anyPolicy ........................48Cooper, et al. Standards Track [Page 2]
RFC 5280 PKIX Certificate and CRL Profile May 2008 4.2.1.15. Freshest CRL (a.k.a. Delta CRL Distribution Point) ......................484.2.2. Private Internet Extensions ........................494.2.2.1. Authority Information Access ..............494.2.2.2. Subject Information Access ................515. CRL and CRL Extensions Profile .................................545.1. CRL Fields ................................................555.1.1. CertificateList Fields .............................565.1.1.1. tbsCertList ...............................565.1.1.2. signatureAlgorithm ........................575.1.1.3. signatureValue ............................575.1.2. Certificate List "To Be Signed" ....................585.1.2.1. Version ...................................585.1.2.2. Signature .................................585.1.2.3. Issuer Name ...............................585.1.2.4. This Update ...............................585.1.2.5. Next Update ...............................595.1.2.6. Revoked Certificates ......................595.1.2.7. Extensions ................................605.2. CRL Extensions ............................................605.2.1. Authority Key Identifier ...........................605.2.2. Issuer Alternative Name ............................605.2.3. CRL Number .........................................615.2.4. Delta CRL Indicator ................................625.2.5. Issuing Distribution Point .........................65 5.2.6. Freshest CRL (a.k.a. Delta CRL Distribution Point) .............................................675.2.7. Authority Information Access .......................675.3. CRL Entry Extensions ......................................695.3.1. Reason Code ........................................695.3.2. Invalidity Date ....................................705.3.3. Certificate Issuer .................................706. Certification Path Validation ..................................716.1. Basic Path Validation .....................................726.1.1. Inputs .............................................756.1.2. Initialization .....................................776.1.3. Basic Certificate Processing .......................806.1.4. Preparation for Certificate i+1 ....................846.1.5. Wrap-Up Procedure ..................................876.1.6. Outputs ............................................896.2. Using the Path Validation Algorithm .......................896.3. CRL Validation ............................................906.3.1. Revocation Inputs ..................................916.3.2. Initialization and Revocation State Variables ......916.3.3. CRL Processing .....................................927. Processing Rules for Internationalized Names ...................957.1. Internationalized Names in Distinguished Names ............967.2. Internationalized Domain Names in GeneralName .............97Cooper, et al. Standards Track [Page 3]
RFC 5280 PKIX Certificate and CRL Profile May 20087.3. Internationalized Domain Names in Distinguished Names .....987.4. Internationalized Resource Identifiers ....................987.5. Internationalized Electronic Mail Addresses ..............1008. Security Considerations .......................................1009. IANA Considerations ...........................................10510. Acknowledgments ..............................................10511. References ...................................................10511.1. Normative References ....................................10511.2. Informative References ..................................107Appendix A. Pseudo-ASN.1 Structures and OIDs ....................110A.1. Explicitly Tagged Module, 1988 Syntax ....................110A.2. Implicitly Tagged Module, 1988 Syntax ....................125Appendix B. ASN.1 Notes ..........................................133Appendix C. Examples .............................................136C.1. RSA Self-Signed Certificate ..............................137C.2. End Entity Certificate Using RSA .........................140C.3. End Entity Certificate Using DSA .........................143C.4. Certificate Revocation List ..............................1471. Introduction This specification is one part of a family of standards for the X.509 Public Key Infrastructure (PKI) for the Internet. This specification profiles the format and semantics of certificates and certificate revocation lists (CRLs) for the Internet PKI. Procedures are described for processing of certification paths in the Internet environment. Finally, ASN.1 modules are provided in the appendices for all data structures defined or referenced. Section 2 describes Internet PKI requirements and the assumptions that affect the scope of this document. Section 3 presents an architectural model and describes its relationship to previous IETF and ISO/IEC/ITU-T standards. In particular, this document's relationship with the IETF PEM specifications and the ISO/IEC/ITU-T X.509 documents is described. Section 4 profiles the X.509 version 3 certificate, and Section 5 profiles the X.509 version 2 CRL. The profiles include the identification of ISO/IEC/ITU-T and ANSI extensions that may be useful in the Internet PKI. The profiles are presented in the 1988 Abstract Syntax Notation One (ASN.1) rather than the 1997 ASN.1 syntax used in the most recent ISO/IEC/ITU-T standards. Section 6 includes certification path validation procedures. These procedures are based upon the ISO/IEC/ITU-T definition. Implementations are REQUIRED to derive the same results but are not required to use the specified procedures. Cooper, et al. Standards Track [Page 4]
RFC 5280 PKIX Certificate and CRL Profile May 2008 Procedures for identification and encoding of public key materials and digital signatures are defined in [RFC3279], [RFC4055], and [RFC4491]. Implementations of this specification are not required to use any particular cryptographic algorithms. However, conforming implementations that use the algorithms identified in [RFC3279], [RFC4055], and [RFC4491] MUST identify and encode the public key materials and digital signatures as described in those specifications. Finally, three appendices are provided to aid implementers. AppendixA contains all ASN.1 structures defined or referenced within this specification. As above, the material is presented in the 1988 ASN.1. Appendix B contains notes on less familiar features of the ASN.1 notation used within this specification. Appendix C contains examples of conforming certificates and a conforming CRL. This specification obsoletes [RFC3280]. Differences from RFC 3280 are summarized below: * Enhanced support for internationalized names is specified in Section 7, with rules for encoding and comparing Internationalized Domain Names, Internationalized Resource Identifiers (IRIs), and distinguished names. These rules are aligned with comparison rules established in current RFCs, including [RFC3490], [RFC3987], and [RFC4518]. * Sections 4.1.2.4 and 4.1.2.6 incorporate the conditions for continued use of legacy text encoding schemes that were specified in [RFC4630]. Where in use by an established PKI, transition to UTF8String could cause denial of service based on name chaining failures or incorrect processing of name constraints. * Section 4.2.1.4 in RFC 3280, which specified the privateKeyUsagePeriod certificate extension but deprecated its use, was removed. Use of this ISO standard extension is neither deprecated nor recommended for use in the Internet PKI. * Section 4.2.1.5 recommends marking the policy mappings extension as critical. RFC 3280 required that the policy mappings extension be marked as non-critical. * Section 4.2.1.11 requires marking the policy constraints extension as critical. RFC 3280 permitted the policy constraints extension to be marked as critical or non-critical. * The Authority Information Access (AIA) CRL extension, as specified in [RFC4325], was added as Section 5.2.7. Cooper, et al. Standards Track [Page 5]
RFC 5280 PKIX Certificate and CRL Profile May 2008 * Sections 5.2 and 5.3 clarify the rules for handling unrecognized CRL extensions and CRL entry extensions, respectively. * Section 5.3.2 in RFC 3280, which specified the holdInstructionCode CRL entry extension, was removed. * The path validation algorithm specified in Section 6 no longer tracks the criticality of the certificate policies extensions in a chain of certificates. In RFC 3280, this information was returned to a relying party. * The Security Considerations section addresses the risk of circular dependencies arising from the use of https or similar schemes in the CRL distribution points, authority information access, or subject information access extensions. * The Security Considerations section addresses risks associated with name ambiguity. * The Security Considerations section references RFC 4210 for procedures to signal changes in CA operations. The ASN.1 modules in Appendix A are unchanged from RFC 3280, except that ub-emailaddress-length was changed from 128 to 255 in order to align with PKCS #9 [RFC2985]. The key words "MUST", "MUST NOT", "REQUIRED", "SHALL", "SHALL NOT", "SHOULD", "SHOULD NOT", "RECOMMENDED", "MAY", and "OPTIONAL" in this document are to be interpreted as described in [RFC2119]. 2. Requirements and Assumptions The goal of this specification is to develop a profile to facilitate the use of X.509 certificates within Internet applications for those communities wishing to make use of X.509 technology. Such applications may include WWW, electronic mail, user authentication, and IPsec. In order to relieve some of the obstacles to using X.509 certificates, this document defines a profile to promote the development of certificate management systems, development of application tools, and interoperability determined by policy. Some communities will need to supplement, or possibly replace, this profile in order to meet the requirements of specialized application domains or environments with additional authorization, assurance, or operational requirements. However, for basic applications, common representations of frequently used attributes are defined so that Cooper, et al. Standards Track [Page 6]
RFC 5280 PKIX Certificate and CRL Profile May 2008 application developers can obtain necessary information without regard to the issuer of a particular certificate or certificate revocation list (CRL). A certificate user should review the certificate policy generated by the certification authority (CA) before relying on the authentication or non-repudiation services associated with the public key in a particular certificate. To this end, this standard does not prescribe legally binding rules or duties. As supplemental authorization and attribute management tools emerge, such as attribute certificates, it may be appropriate to limit the authenticated attributes that are included in a certificate. These other management tools may provide more appropriate methods of conveying many authenticated attributes. 2.1. Communication and Topology The users of certificates will operate in a wide range of environments with respect to their communication topology, especially users of secure electronic mail. This profile supports users without high bandwidth, real-time IP connectivity, or high connection availability. In addition, the profile allows for the presence of firewall or other filtered communication. This profile does not assume the deployment of an X.500 directory system [X.500] or a Lightweight Directory Access Protocol (LDAP) directory system [RFC4510]. The profile does not prohibit the use of an X.500 directory or an LDAP directory; however, any means of distributing certificates and certificate revocation lists (CRLs) may be used. 2.2. Acceptability Criteria The goal of the Internet Public Key Infrastructure (PKI) is to meet the needs of deterministic, automated identification, authentication, access control, and authorization functions. Support for these services determines the attributes contained in the certificate as well as the ancillary control information in the certificate such as policy data and certification path constraints. 2.3. User Expectations Users of the Internet PKI are people and processes who use client software and are the subjects named in certificates. These uses include readers and writers of electronic mail, the clients for WWW browsers, WWW servers, and the key manager for IPsec within a router. This profile recognizes the limitations of the platforms these users Cooper, et al. Standards Track [Page 7]
RFC 5280 PKIX Certificate and CRL Profile May 2008 employ and the limitations in sophistication and attentiveness of the users themselves. This manifests itself in minimal user configuration responsibility (e.g., trusted CA keys, rules), explicit platform usage constraints within the certificate, certification path constraints that shield the user from many malicious actions, and applications that sensibly automate validation functions. 2.4. Administrator Expectations As with user expectations, the Internet PKI profile is structured to support the individuals who generally operate CAs. Providing administrators with unbounded choices increases the chances that a subtle CA administrator mistake will result in broad compromise. Also, unbounded choices greatly complicate the software that process and validate the certificates created by the CA. 3. Overview of Approach Following is a simplified view of the architectural model assumed by the Public-Key Infrastructure using X.509 (PKIX) specifications. The components in this model are: end entity: user of PKI certificates and/or end user system that is the subject of a certificate; CA: certification authority; RA: registration authority, i.e., an optional system to which a CA delegates certain management functions; CRL issuer: a system that generates and signs CRLs; and repository: a system or collection of distributed systems that stores certificates and CRLs and serves as a means of distributing these certificates and CRLs to end entities. CAs are responsible for indicating the revocation status of the certificates that they issue. Revocation status information may be provided using the Online Certificate Status Protocol (OCSP) [RFC2560], certificate revocation lists (CRLs), or some other mechanism. In general, when revocation status information is provided using CRLs, the CA is also the CRL issuer. However, a CA may delegate the responsibility for issuing CRLs to a different entity. Note that an Attribute Authority (AA) might also choose to delegate the publication of CRLs to a CRL issuer. Cooper, et al. Standards Track [Page 8]
RFC 5280 PKIX Certificate and CRL Profile May 2008PKI Entities 3.1. X.509 Version 3 Certificate Users of a public key require confidence that the associated private key is owned by the correct remote subject (person or system) with which an encryption or digital signature mechanism will be used. This confidence is obtained through the use of public key certificates, which are data structures that bind public key values to subjects. The binding is asserted by having a trusted CA digitally sign each certificate. The CA may base this assertion upon technical means (a.k.a., proof of possession through a challenge- response protocol), presentation of the private key, or on an assertion by the subject. A certificate has a limited valid lifetime, which is indicated in its signed contents. Because a certificate's signature and timeliness can be independently checked by a certificate-using client, certificates can be distributed via Cooper, et al. Standards Track [Page 9]
RFC 5280 PKIX Certificate and CRL Profile May 2008 untrusted communications and server systems, and can be cached in unsecured storage in certificate-using systems. ITU-T X.509 (formerly CCITT X.509) or ISO/IEC 9594-8, which was first published in 1988 as part of the X.500 directory recommendations, defines a standard certificate format [X.509]. The certificate format in the 1988 standard is called the version 1 (v1) format. When X.500 was revised in 1993, two more fields were added, resulting in the version 2 (v2) format. The Internet Privacy Enhanced Mail (PEM) RFCs, published in 1993, include specifications for a public key infrastructure based on X.509 v1 certificates [RFC1422]. The experience gained in attempts to deploy RFC 1422 made it clear that the v1 and v2 certificate formats were deficient in several respects. Most importantly, more fields were needed to carry information that PEM design and implementation experience had proven necessary. In response to these new requirements, the ISO/IEC, ITU-T, and ANSI X9 developed the X.509 version 3 (v3) certificate format. The v3 format extends the v2 format by adding provision for additional extension fields. Particular extension field types may be specified in standards or may be defined and registered by any organization or community. In June 1996, standardization of the basic v3 format was completed [X.509]. ISO/IEC, ITU-T, and ANSI X9 have also developed standard extensions for use in the v3 extensions field [X.509][X9.55]. These extensions can convey such data as additional subject identification information, key attribute information, policy information, and certification path constraints. However, the ISO/IEC, ITU-T, and ANSI X9 standard extensions are very broad in their applicability. In order to develop interoperable implementations of X.509 v3 systems for Internet use, it is necessary to specify a profile for use of the X.509 v3 extensions tailored for the Internet. It is one goal of this document to specify a profile for Internet WWW, electronic mail, and IPsec applications. Environments with additional requirements may build on this profile or may replace it. 3.2. Certification Paths and Trust A user of a security service requiring knowledge of a public key generally needs to obtain and validate a certificate containing the required public key. If the public key user does not already hold an assured copy of the public key of the CA that signed the certificate, the CA's name, and related information (such as the validity period or name constraints), then it might need an additional certificate to obtain that public key. In general, a chain of multiple certificates Cooper, et al. Standards Track [Page 10]
RFC 5280 PKIX Certificate and CRL Profile May 2008 may be needed, comprising a certificate of the public key owner (the end entity) signed by one CA, and zero or more additional certificates of CAs signed by other CAs. Such chains, called certification paths, are required because a public key user is only initialized with a limited number of assured CA public keys. There are different ways in which CAs might be configured in order for public key users to be able to find certification paths. For PEM, RFC 1422 defined a rigid hierarchical structure of CAs. There are three types of PEM certification authority: (a) Internet Policy Registration Authority (IPRA): This authority, operated under the auspices of the Internet Society, acts as the root of the PEM certification hierarchy at level 1. It issues certificates only for the next level of authorities, PCAs. All certification paths start with the IPRA. (b) Policy Certification Authorities (PCAs): PCAs are at level 2 of the hierarchy, each PCA being certified by the IPRA. A PCA shall establish and publish a statement of its policy with respect to certifying users or subordinate certification authorities. Distinct PCAs aim to satisfy different user needs. For example, one PCA (an organizational PCA) might support the general electronic mail needs of commercial organizations, and another PCA (a high-assurance PCA) might have a more stringent policy designed for satisfying legally binding digital signature requirements. (c) Certification Authorities (CAs): CAs are at level 3 of the hierarchy and can also be at lower levels. Those at level 3 are certified by PCAs. CAs represent, for example, particular organizations, particular organizational units (e.g., departments, groups, sections), or particular geographical areas. RFC 1422 furthermore has a name subordination rule, which requires that a CA can only issue certificates for entities whose names are subordinate (in the X.500 naming tree) to the name of the CA itself. The trust associated with a PEM certification path is implied by the PCA name. The name subordination rule ensures that CAs below the PCA are sensibly constrained as to the set of subordinate entities they can certify (e.g., a CA for an organization can only certify entities in that organization's name tree). Certificate user systems are able to mechanically check that the name subordination rule has been followed. Cooper, et al. Standards Track [Page 11]
RFC 5280 PKIX Certificate and CRL Profile May 2008RFC 1422 uses the X.509 v1 certificate format. The limitations of X.509 v1 required imposition of several structural restrictions to clearly associate policy information or restrict the utility of certificates. These restrictions included: (a) a pure top-down hierarchy, with all certification paths starting from IPRA; (b) a naming subordination rule restricting the names of a CA's subjects; and (c) use of the PCA concept, which requires knowledge of individual PCAs to be built into certificate chain verification logic. Knowledge of individual PCAs was required to determine if a chain could be accepted. With X.509 v3, most of the requirements addressed by RFC 1422 can be addressed using certificate extensions, without a need to restrict the CA structures used. In particular, the certificate extensions relating to certificate policies obviate the need for PCAs and the constraint extensions obviate the need for the name subordination rule. As a result, this document supports a more flexible architecture, including: (a) Certification paths start with a public key of a CA in a user's own domain, or with the public key of the top of a hierarchy. Starting with the public key of a CA in a user's own domain has certain advantages. In some environments, the local domain is the most trusted. (b) Name constraints may be imposed through explicit inclusion of a name constraints extension in a certificate, but are not required. (c) Policy extensions and policy mappings replace the PCA concept, which permits a greater degree of automation. The application can determine if the certification path is acceptable based on the contents of the certificates instead of a priori knowledge of PCAs. This permits automation of certification path processing. X.509 v3 also includes an extension that identifies the subject of a certificate as being either a CA or an end entity, reducing the reliance on out-of-band information demanded in PEM. This specification covers two classes of certificates: CA certificates and end entity certificates. CA certificates may be further divided into three classes: cross-certificates, self-issued Cooper, et al. Standards Track [Page 12]
RFC 5280 PKIX Certificate and CRL Profile May 2008 certificates, and self-signed certificates. Cross-certificates are CA certificates in which the issuer and subject are different entities. Cross-certificates describe a trust relationship between the two CAs. Self-issued certificates are CA certificates in which the issuer and subject are the same entity. Self-issued certificates are generated to support changes in policy or operations. Self- signed certificates are self-issued certificates where the digital signature may be verified by the public key bound into the certificate. Self-signed certificates are used to convey a public key for use to begin certification paths. End entity certificates are issued to subjects that are not authorized to issue certificates. 3.3. Revocation When a certificate is issued, it is expected to be in use for its entire validity period. However, various circumstances may cause a certificate to become invalid prior to the expiration of the validity period. Such circumstances include change of name, change of association between subject and CA (e.g., an employee terminates employment with an organization), and compromise or suspected compromise of the corresponding private key. Under such circumstances, the CA needs to revoke the certificate. X.509 defines one method of certificate revocation. This method involves each CA periodically issuing a signed data structure called a certificate revocation list (CRL). A CRL is a time-stamped list identifying revoked certificates that is signed by a CA or CRL issuer and made freely available in a public repository. Each revoked certificate is identified in a CRL by its certificate serial number. When a certificate-using system uses a certificate (e.g., for verifying a remote user's digital signature), that system not only checks the certificate signature and validity but also acquires a suitably recent CRL and checks that the certificate serial number is not on that CRL. The meaning of "suitably recent" may vary with local policy, but it usually means the most recently issued CRL. A new CRL is issued on a regular periodic basis (e.g., hourly, daily, or weekly). An entry is added to the CRL as part of the next update following notification of revocation. An entry MUST NOT be removed from the CRL until it appears on one regularly scheduled CRL issued beyond the revoked certificate's validity period. An advantage of this revocation method is that CRLs may be distributed by exactly the same means as certificates themselves, namely, via untrusted servers and untrusted communications. One limitation of the CRL revocation method, using untrusted communications and servers, is that the time granularity of revocation is limited to the CRL issue period. For example, if a Cooper, et al. Standards Track [Page 13]
RFC 5280 PKIX Certificate and CRL Profile May 2008 revocation is reported now, that revocation will not be reliably notified to certificate-using systems until all currently issued CRLs are scheduled to be updated -- this may be up to one hour, one day, or one week depending on the frequency that CRLs are issued. As with the X.509 v3 certificate format, in order to facilitate interoperable implementations from multiple vendors, the X.509 v2 CRL format needs to be profiled for Internet use. It is one goal of this document to specify that profile. However, this profile does not require the issuance of CRLs. Message formats and protocols supporting on-line revocation notification are defined in other PKIX specifications. On-line methods of revocation notification may be applicable in some environments as an alternative to the X.509 CRL. On-line revocation checking may significantly reduce the latency between a revocation report and the distribution of the information to relying parties. Once the CA accepts a revocation report as authentic and valid, any query to the on-line service will correctly reflect the certificate validation impacts of the revocation. However, these methods impose new security requirements: the certificate validator needs to trust the on-line validation service while the repository does not need to be trusted. 3.4. Operational Protocols Operational protocols are required to deliver certificates and CRLs (or status information) to certificate-using client systems. Provisions are needed for a variety of different means of certificate and CRL delivery, including distribution procedures based on LDAP, HTTP, FTP, and X.500. Operational protocols supporting these functions are defined in other PKIX specifications. These specifications may include definitions of message formats and procedures for supporting all of the above operational environments, including definitions of or references to appropriate MIME content types. 3.5. Management Protocols Management protocols are required to support on-line interactions between PKI user and management entities. For example, a management protocol might be used between a CA and a client system with which a key pair is associated, or between two CAs that cross-certify each other. The set of functions that potentially need to be supported by management protocols include: (a) registration: This is the process whereby a user first makes itself known to a CA (directly, or through an RA), prior to that CA issuing a certificate or certificates for that user. Cooper, et al. Standards Track [Page 14]
RFC 5280 PKIX Certificate and CRL Profile May 2008 (b) initialization: Before a client system can operate securely, it is necessary to install key materials that have the appropriate relationship with keys stored elsewhere in the infrastructure. For example, the client needs to be securely initialized with the public key and other assured information of the trusted CA(s), to be used in validating certificate paths. Furthermore, a client typically needs to be initialized with its own key pair(s). (c) certification: This is the process in which a CA issues a certificate for a user's public key, and returns that certificate to the user's client system and/or posts that certificate in a repository. (d) key pair recovery: As an option, user client key materials (e.g., a user's private key used for encryption purposes) may be backed up by a CA or a key backup system. If a user needs to recover these backed-up key materials (e.g., as a result of a forgotten password or a lost key chain file), an on-line protocol exchange may be needed to support such recovery. (e) key pair update: All key pairs need to be updated regularly, i.e., replaced with a new key pair, and new certificates issued. (f) revocation request: An authorized person advises a CA of an abnormal situation requiring certificate revocation. (g) cross-certification: Two CAs exchange information used in establishing a cross-certificate. A cross-certificate is a certificate issued by one CA to another CA that contains a CA signature key used for issuing certificates. Note that on-line protocols are not the only way of implementing the above functions. For all functions, there are off-line methods of achieving the same result, and this specification does not mandate use of on-line protocols. For example, when hardware tokens are used, many of the functions may be achieved as part of the physical token delivery. Furthermore, some of the above functions may be combined into one protocol exchange. In particular, two or more of the registration, initialization, and certification functions can be combined into one protocol exchange. Cooper, et al. Standards Track [Page 15]
RFC 5280 PKIX Certificate and CRL Profile May 2008 The PKIX series of specifications defines a set of standard message formats supporting the above functions. The protocols for conveying these messages in different environments (e.g., email, file transfer, and WWW) are described in those specifications. 4. Certificate and Certificate Extensions Profile This section presents a profile for public key certificates that will foster interoperability and a reusable PKI. This section is based upon the X.509 v3 certificate format and the standard certificate extensions defined in [X.509]. The ISO/IEC and ITU-T documents use the 1997 version of ASN.1; while this document uses the 1988 ASN.1 syntax, the encoded certificate and standard extensions are equivalent. This section also defines private extensions required to support a PKI for the Internet community. Certificates may be used in a wide range of applications and environments covering a broad spectrum of interoperability goals and a broader spectrum of operational and assurance requirements. The goal of this document is to establish a common baseline for generic applications requiring broad interoperability and limited special purpose requirements. In particular, the emphasis will be on supporting the use of X.509 v3 certificates for informal Internet electronic mail, IPsec, and WWW applications. 4.1. Basic Certificate Fields The X.509 v3 certificate basic syntax is as follows. For signature calculation, the data that is to be signed is encoded using the ASN.1 distinguished encoding rules (DER) [X.690]. ASN.1 DER encoding is a tag, length, value encoding system for each element. Certificate ::= SEQUENCE { tbsCertificate TBSCertificate, signatureAlgorithm AlgorithmIdentifier, signatureValue BIT STRING } TBSCertificate ::= SEQUENCE { version [0] EXPLICIT Version DEFAULT v1, serialNumber CertificateSerialNumber, signature AlgorithmIdentifier, issuer Name, validity Validity, subject Name, subjectPublicKeyInfo SubjectPublicKeyInfo, issuerUniqueID [1] IMPLICIT UniqueIdentifier OPTIONAL, -- If present, version MUST be v2 or v3 Cooper, et al. Standards Track [Page 16]
RFC 5280 PKIX Certificate and CRL Profile May 2008 subjectUniqueID [2] IMPLICIT UniqueIdentifier OPTIONAL, -- If present, version MUST be v2 or v3 extensions [3] EXPLICIT Extensions OPTIONAL -- If present, version MUST be v3 } Version ::= INTEGER { v1(0), v2(1), v3(2) } CertificateSerialNumber ::= INTEGER Validity ::= SEQUENCE { notBefore Time, notAfter Time } Time ::= CHOICE { utcTime UTCTime, generalTime GeneralizedTime } UniqueIdentifier ::= BIT STRING SubjectPublicKeyInfo ::= SEQUENCE { algorithm AlgorithmIdentifier, subjectPublicKey BIT STRING } Extensions ::= SEQUENCE SIZE (1..MAX) OF Extension Extension ::= SEQUENCE { extnID OBJECT IDENTIFIER, critical BOOLEAN DEFAULT FALSE, extnValue OCTET STRING -- contains the DER encoding of an ASN.1 value -- corresponding to the extension type identified -- by extnID } The following items describe the X.509 v3 certificate for use in the Internet. 4.1.1. Certificate Fields The Certificate is a SEQUENCE of three required fields. The fields are described in detail in the following subsections. Cooper, et al. Standards Track [Page 17]
RFC 5280 PKIX Certificate and CRL Profile May 20084.1.1.1. tbsCertificate The field contains the names of the subject and issuer, a public key associated with the subject, a validity period, and other associated information. The fields are described in detail in Section 4.1.2; the tbsCertificate usually includes extensions, which are described in Section 4.2. 4.1.1.2. signatureAlgorithm The signatureAlgorithm field contains the identifier for the cryptographic algorithm used by the CA to sign this certificate. [RFC3279], [RFC4055], and [RFC4491] list supported signature algorithms, but other signature algorithms MAY also be supported. An algorithm identifier is defined by the following ASN.1 structure: AlgorithmIdentifier ::= SEQUENCE { algorithm OBJECT IDENTIFIER, parameters ANY DEFINED BY algorithm OPTIONAL } The algorithm identifier is used to identify a cryptographic algorithm. The OBJECT IDENTIFIER component identifies the algorithm (such as DSA with SHA-1). The contents of the optional parameters field will vary according to the algorithm identified. This field MUST contain the same algorithm identifier as the signature field in the sequence tbsCertificate (Section 4.1.2.3). 4.1.1.3. signatureValue The signatureValue field contains a digital signature computed upon the ASN.1 DER encoded tbsCertificate. The ASN.1 DER encoded tbsCertificate is used as the input to the signature function. This signature value is encoded as a BIT STRING and included in the signature field. The details of this process are specified for each of the algorithms listed in [RFC3279], [RFC4055], and [RFC4491]. By generating this signature, a CA certifies the validity of the information in the tbsCertificate field. In particular, the CA certifies the binding between the public key material and the subject of the certificate. 4.1.2. TBSCertificate The sequence TBSCertificate contains information associated with the subject of the certificate and the CA that issued it. Every TBSCertificate contains the names of the subject and issuer, a public Cooper, et al. Standards Track [Page 18]
RFC 5280 PKIX Certificate and CRL Profile May 2008 key associated with the subject, a validity period, a version number, and a serial number; some MAY contain optional unique identifier fields. The remainder of this section describes the syntax and semantics of these fields. A TBSCertificate usually includes extensions. Extensions for the Internet PKI are described in Section4.2. 4.1.2.1. Version This field describes the version of the encoded certificate. When extensions are used, as expected in this profile, version MUST be 3 (value is 2). If no extensions are present, but a UniqueIdentifier is present, the version SHOULD be 2 (value is 1); however, the version MAY be 3. If only basic fields are present, the version SHOULD be 1 (the value is omitted from the certificate as the default value); however, the version MAY be 2 or 3. Implementations SHOULD be prepared to accept any version certificate. At a minimum, conforming implementations MUST recognize version 3 certificates. Generation of version 2 certificates is not expected by implementations based on this profile. 4.1.2.2. Serial Number The serial number MUST be a positive integer assigned by the CA to each certificate. It MUST be unique for each certificate issued by a given CA (i.e., the issuer name and serial number identify a unique certificate). CAs MUST force the serialNumber to be a non-negative integer. Given the uniqueness requirements above, serial numbers can be expected to contain long integers. Certificate users MUST be able to handle serialNumber values up to 20 octets. Conforming CAs MUST NOT use serialNumber values longer than 20 octets. Note: Non-conforming CAs may issue certificates with serial numbers that are negative or zero. Certificate users SHOULD be prepared to gracefully handle such certificates. 4.1.2.3. Signature This field contains the algorithm identifier for the algorithm used by the CA to sign the certificate. This field MUST contain the same algorithm identifier as the signatureAlgorithm field in the sequence Certificate (Section Cooper, et al. Standards Track [Page 19]
RFC 5280 PKIX Certificate and CRL Profile May 2008 4.1.1.2). The contents of the optional parameters field will vary according to the algorithm identified. [RFC3279], [RFC4055], and [RFC4491] list supported signature algorithms, but other signature algorithms MAY also be supported. 4.1.2.4. Issuer The issuer field identifies the entity that has signed and issued the certificate. The issuer field MUST contain a non-empty distinguished name (DN). The issuer field is defined as the X.501 type Name [X.501]. Name is defined by the following ASN.1 structures: Name ::= CHOICE { -- only one possibility for now -- rdnSequence RDNSequence } RDNSequence ::= SEQUENCE OF RelativeDistinguishedName RelativeDistinguishedName ::= SET SIZE (1..MAX) OF AttributeTypeAndValue AttributeTypeAndValue ::= SEQUENCE { type AttributeType, value AttributeValue } AttributeType ::= OBJECT IDENTIFIER AttributeValue ::= ANY -- DEFINED BY AttributeType DirectoryString ::= CHOICE { teletexString TeletexString (SIZE (1..MAX)), printableString PrintableString (SIZE (1..MAX)), universalString UniversalString (SIZE (1..MAX)), utf8String UTF8String (SIZE (1..MAX)), bmpString BMPString (SIZE (1..MAX)) } The Name describes a hierarchical name composed of attributes, such as country name, and corresponding values, such as US. The type of the component AttributeValue is determined by the AttributeType; in general it will be a DirectoryString. The DirectoryString type is defined as a choice of PrintableString, TeletexString, BMPString, UTF8String, and UniversalString. CAs conforming to this profile MUST use either the PrintableString or UTF8String encoding of DirectoryString, with two exceptions. When CAs have previously issued certificates with issuer fields with attributes encoded using TeletexString, BMPString, or UniversalString, then the CA MAY continue to use these encodings of the DirectoryString to preserve backward compatibility. Also, new Cooper, et al. Standards Track [Page 20]
RFC 5280 PKIX Certificate and CRL Profile May 2008 CAs that are added to a domain where existing CAs issue certificates with issuer fields with attributes encoded using TeletexString, BMPString, or UniversalString MAY encode attributes that they share with the existing CAs using the same encodings as the existing CAs use. As noted above, distinguished names are composed of attributes. This specification does not restrict the set of attribute types that may appear in names. However, conforming implementations MUST be prepared to receive certificates with issuer names containing the set of attribute types defined below. This specification RECOMMENDS support for additional attribute types. Standard sets of attributes have been defined in the X.500 series of specifications [X.520]. Implementations of this specification MUST be prepared to receive the following standard attribute types in issuer and subject (Section 4.1.2.6) names: * country, * organization, * organizational unit, * distinguished name qualifier, * state or province name, * common name (e.g., "Susan Housley"), and * serial number. In addition, implementations of this specification SHOULD be prepared to receive the following standard attribute types in issuer and subject names: * locality, * title, * surname, * given name, * initials, * pseudonym, and * generation qualifier (e.g., "Jr.", "3rd", or "IV"). The syntax and associated object identifiers (OIDs) for these attribute types are provided in the ASN.1 modules in Appendix A. In addition, implementations of this specification MUST be prepared to receive the domainComponent attribute, as defined in [RFC4519]. The Domain Name System (DNS) provides a hierarchical resource labeling system. This attribute provides a convenient mechanism for organizations that wish to use DNs that parallel their DNS names. This is not a replacement for the dNSName component of the alternative name extensions. Implementations are not required to Cooper, et al. Standards Track [Page 21]
RFC 5280 PKIX Certificate and CRL Profile May 2008 convert such names into DNS names. The syntax and associated OID for this attribute type are provided in the ASN.1 modules in Appendix A. Rules for encoding internationalized domain names for use with the domainComponent attribute type are specified in Section 7.3. Certificate users MUST be prepared to process the issuer distinguished name and subject distinguished name (Section 4.1.2.6) fields to perform name chaining for certification path validation (Section 6). Name chaining is performed by matching the issuer distinguished name in one certificate with the subject name in a CA certificate. Rules for comparing distinguished names are specified in Section 7.1. If the names in the issuer and subject field in a certificate match according to the rules specified in Section 7.1, then the certificate is self-issued. 4.1.2.5. Validity The certificate validity period is the time interval during which the CA warrants that it will maintain information about the status of the certificate. The field is represented as a SEQUENCE of two dates: the date on which the certificate validity period begins (notBefore) and the date on which the certificate validity period ends (notAfter). Both notBefore and notAfter may be encoded as UTCTime or GeneralizedTime. CAs conforming to this profile MUST always encode certificate validity dates through the year 2049 as UTCTime; certificate validity dates in 2050 or later MUST be encoded as GeneralizedTime. Conforming applications MUST be able to process validity dates that are encoded in either UTCTime or GeneralizedTime. The validity period for a certificate is the period of time from notBefore through notAfter, inclusive. In some situations, devices are given certificates for which no good expiration date can be assigned. For example, a device could be issued a certificate that binds its model and serial number to its public key; such a certificate is intended to be used for the entire lifetime of the device. To indicate that a certificate has no well-defined expiration date, the notAfter SHOULD be assigned the GeneralizedTime value of 99991231235959Z. When the issuer will not be able to maintain status information until the notAfter date (including when the notAfter date is 99991231235959Z), the issuer MUST ensure that no valid certification path exists for the certificate after maintenance of status Cooper, et al. Standards Track [Page 22]
RFC 5280 PKIX Certificate and CRL Profile May 2008 information is terminated. This may be accomplished by expiration or revocation of all CA certificates containing the public key used to verify the signature on the certificate and discontinuing use of the public key used to verify the signature on the certificate as a trust anchor. 4.1.2.5.1. UTCTime The universal time type, UTCTime, is a standard ASN.1 type intended for representation of dates and time. UTCTime specifies the year through the two low-order digits and time is specified to the precision of one minute or one second. UTCTime includes either Z (for Zulu, or Greenwich Mean Time) or a time differential. For the purposes of this profile, UTCTime values MUST be expressed in Greenwich Mean Time (Zulu) and MUST include seconds (i.e., times are YYMMDDHHMMSSZ), even where the number of seconds is zero. Conforming systems MUST interpret the year field (YY) as follows: Where YY is greater than or equal to 50, the year SHALL be interpreted as 19YY; and Where YY is less than 50, the year SHALL be interpreted as 20YY. 4.1.2.5.2. GeneralizedTime The generalized time type, GeneralizedTime, is a standard ASN.1 type for variable precision representation of time. Optionally, the GeneralizedTime field can include a representation of the time differential between local and Greenwich Mean Time. For the purposes of this profile, GeneralizedTime values MUST be expressed in Greenwich Mean Time (Zulu) and MUST include seconds (i.e., times are YYYYMMDDHHMMSSZ), even where the number of seconds is zero. GeneralizedTime values MUST NOT include fractional seconds. 4.1.2.6. Subject The subject field identifies the entity associated with the public key stored in the subject public key field. The subject name MAY be carried in the subject field and/or the subjectAltName extension. If the subject is a CA (e.g., the basic constraints extension, as discussed in Section 4.2.1.9, is present and the value of cA is TRUE), then the subject field MUST be populated with a non-empty distinguished name matching the contents of the issuer field (Section4.1.2.4) in all certificates issued by the subject CA. If the subject is a CRL issuer (e.g., the key usage extension, as discussed in Section 4.2.1.3, is present and the value of cRLSign is TRUE), Cooper, et al. Standards Track [Page 23]
RFC 5280 PKIX Certificate and CRL Profile May 2008 then the subject field MUST be populated with a non-empty distinguished name matching the contents of the issuer field (Section5.1.2.3) in all CRLs issued by the subject CRL issuer. If subject naming information is present only in the subjectAltName extension (e.g., a key bound only to an email address or URI), then the subject name MUST be an empty sequence and the subjectAltName extension MUST be critical. Where it is non-empty, the subject field MUST contain an X.500 distinguished name (DN). The DN MUST be unique for each subject entity certified by the one CA as defined by the issuer field. A CA MAY issue more than one certificate with the same DN to the same subject entity. The subject field is defined as the X.501 type Name. Implementation requirements for this field are those defined for the issuer field (Section 4.1.2.4). Implementations of this specification MUST be prepared to receive subject names containing the attribute types required for the issuer field. Implementations of this specification SHOULD be prepared to receive subject names containing the recommended attribute types for the issuer field. The syntax and associated object identifiers (OIDs) for these attribute types are provided in the ASN.1 modules in Appendix A. Implementations of this specification MAY use the comparison rules in Section 7.1 to process unfamiliar attribute types (i.e., for name chaining) whose attribute values use one of the encoding options from DirectoryString. Binary comparison should be used when unfamiliar attribute types include attribute values with encoding options other than those found in DirectoryString. This allows implementations to process certificates with unfamiliar attributes in the subject name. When encoding attribute values of type DirectoryString, conforming CAs MUST use PrintableString or UTF8String encoding, with the following exceptions: (a) When the subject of the certificate is a CA, the subject field MUST be encoded in the same way as it is encoded in the issuer field (Section 4.1.2.4) in all certificates issued by the subject CA. Thus, if the subject CA encodes attributes in the issuer fields of certificates that it issues using the TeletexString, BMPString, or UniversalString encodings, then the subject field of certificates issued to that CA MUST use the same encoding. (b) When the subject of the certificate is a CRL issuer, the subject field MUST be encoded in the same way as it is encoded in the issuer field (Section 5.1.2.3) in all CRLs issued by the subject CRL issuer. Cooper, et al. Standards Track [Page 24]
RFC 5280 PKIX Certificate and CRL Profile May 2008 (c) TeletexString, BMPString, and UniversalString are included for backward compatibility, and SHOULD NOT be used for certificates for new subjects. However, these types MAY be used in certificates where the name was previously established, including cases in which a new certificate is being issued to an existing subject or a certificate is being issued to a new subject where the attributes being encoded have been previously established in certificates issued to other subjects. Certificate users SHOULD be prepared to receive certificates with these types. Legacy implementations exist where an electronic mail address is embedded in the subject distinguished name as an emailAddress attribute [RFC2985]. The attribute value for emailAddress is of type IA5String to permit inclusion of the character '@', which is not part of the PrintableString character set. emailAddress attribute values are not case-sensitive (e.g., "subscriber@example.com" is the same as "SUBSCRIBER@EXAMPLE.COM"). Conforming implementations generating new certificates with electronic mail addresses MUST use the rfc822Name in the subject alternative name extension (Section 4.2.1.6) to describe such identities. Simultaneous inclusion of the emailAddress attribute in the subject distinguished name to support legacy implementations is deprecated but permitted. 4.1.2.7. Subject Public Key Info This field is used to carry the public key and identify the algorithm with which the key is used (e.g., RSA, DSA, or Diffie-Hellman). The algorithm is identified using the AlgorithmIdentifier structure specified in Section 4.1.1.2. The object identifiers for the supported algorithms and the methods for encoding the public key materials (public key and parameters) are specified in [RFC3279], [RFC4055], and [RFC4491]. 4.1.2.8. Unique Identifiers These fields MUST only appear if the version is 2 or 3 (Section4.1.2.1). These fields MUST NOT appear if the version is 1. The subject and issuer unique identifiers are present in the certificate to handle the possibility of reuse of subject and/or issuer names over time. This profile RECOMMENDS that names not be reused for different entities and that Internet certificates not make use of unique identifiers. CAs conforming to this profile MUST NOT generate certificates with unique identifiers. Applications conforming to Cooper, et al. Standards Track [Page 25]
RFC 5280 PKIX Certificate and CRL Profile May 2008 this profile SHOULD be capable of parsing certificates that include unique identifiers, but there are no processing requirements associated with the unique identifiers. 4.1.2.9. Extensions This field MUST only appear if the version is 3 (Section 4.1.2.1). If present, this field is a SEQUENCE of one or more certificate extensions. The format and content of certificate extensions in the Internet PKI are defined in Section 4.2. 4.2. Certificate Extensions The extensions defined for X.509 v3 certificates provide methods for associating additional attributes with users or public keys and for managing relationships between CAs. The X.509 v3 certificate format also allows communities to define private extensions to carry information unique to those communities. Each extension in a certificate is designated as either critical or non-critical. A certificate-using system MUST reject the certificate if it encounters a critical extension it does not recognize or a critical extension that contains information that it cannot process. A non-critical extension MAY be ignored if it is not recognized, but MUST be processed if it is recognized. The following sections present recommended extensions used within Internet certificates and standard locations for information. Communities may elect to use additional extensions; however, caution ought to be exercised in adopting any critical extensions in certificates that might prevent use in a general context. Each extension includes an OID and an ASN.1 structure. When an extension appears in a certificate, the OID appears as the field extnID and the corresponding ASN.1 DER encoded structure is the value of the octet string extnValue. A certificate MUST NOT include more than one instance of a particular extension. For example, a certificate may contain only one authority key identifier extension (Section 4.2.1.1). An extension includes the boolean critical, with a default value of FALSE. The text for each extension specifies the acceptable values for the critical field for CAs conforming to this profile. Conforming CAs MUST support key identifiers (Sections 4.2.1.1 and 4.2.1.2), basic constraints (Section 4.2.1.9), key usage (Section4.2.1.3), and certificate policies (Section 4.2.1.4) extensions. If the CA issues certificates with an empty sequence for the subject field, the CA MUST support the subject alternative name extension (Section 4.2.1.6). Support for the remaining extensions is OPTIONAL. Conforming CAs MAY support extensions that are not identified within Cooper, et al. Standards Track [Page 26]
RFC 5280 PKIX Certificate and CRL Profile May 2008 this specification; certificate issuers are cautioned that marking such extensions as critical may inhibit interoperability. At a minimum, applications conforming to this profile MUST recognize the following extensions: key usage (Section 4.2.1.3), certificate policies (Section 4.2.1.4), subject alternative name (Section4.2.1.6), basic constraints (Section 4.2.1.9), name constraints (Section 4.2.1.10), policy constraints (Section 4.2.1.11), extended key usage (Section 4.2.1.12), and inhibit anyPolicy (Section4.2.1.14). In addition, applications conforming to this profile SHOULD recognize the authority and subject key identifier (Sections 4.2.1.1 and 4.2.1.2) and policy mappings (Section 4.2.1.5) extensions. 4.2.1. Standard Extensions This section identifies standard certificate extensions defined in [X.509] for use in the Internet PKI. Each extension is associated with an OID defined in [X.509]. These OIDs are members of the id-ce arc, which is defined by the following: id-ce OBJECT IDENTIFIER ::= { joint-iso-ccitt(2) ds(5) 29 } 4.2.1.1. Authority Key Identifier The authority key identifier extension provides a means of identifying the public key corresponding to the private key used to sign a certificate. This extension is used where an issuer has multiple signing keys (either due to multiple concurrent key pairs or due to changeover). The identification MAY be based on either the key identifier (the subject key identifier in the issuer's certificate) or the issuer name and serial number. The keyIdentifier field of the authorityKeyIdentifier extension MUST be included in all certificates generated by conforming CAs to facilitate certification path construction. There is one exception; where a CA distributes its public key in the form of a "self-signed" certificate, the authority key identifier MAY be omitted. The signature on a self-signed certificate is generated with the private key associated with the certificate's subject public key. (This proves that the issuer possesses both the public and private keys.) In this case, the subject and authority key identifiers would be identical, but only the subject key identifier is needed for certification path building. The value of the keyIdentifier field SHOULD be derived from the public key used to verify the certificate's signature or a method Cooper, et al. Standards Track [Page 27]
RFC 5280 PKIX Certificate and CRL Profile May 2008 that generates unique values. Two common methods for generating key identifiers from the public key are described in Section 4.2.1.2. Where a key identifier has not been previously established, this specification RECOMMENDS use of one of these methods for generating keyIdentifiers or use of a similar method that uses a different hash algorithm. Where a key identifier has been previously established, the CA SHOULD use the previously established identifier. This profile RECOMMENDS support for the key identifier method by all certificate users. Conforming CAs MUST mark this extension as non-critical. id-ce-authorityKeyIdentifier OBJECT IDENTIFIER ::= { id-ce 35 } AuthorityKeyIdentifier ::= SEQUENCE { keyIdentifier [0] KeyIdentifier OPTIONAL, authorityCertIssuer [1] GeneralNames OPTIONAL, authorityCertSerialNumber [2] CertificateSerialNumber OPTIONAL } KeyIdentifier ::= OCTET STRING 4.2.1.2. Subject Key Identifier The subject key identifier extension provides a means of identifying certificates that contain a particular public key. To facilitate certification path construction, this extension MUST appear in all conforming CA certificates, that is, all certificates including the basic constraints extension (Section 4.2.1.9) where the value of cA is TRUE. In conforming CA certificates, the value of the subject key identifier MUST be the value placed in the key identifier field of the authority key identifier extension (Section 4.2.1.1) of certificates issued by the subject of this certificate. Applications are not required to verify that key identifiers match when performing certification path validation. For CA certificates, subject key identifiers SHOULD be derived from the public key or a method that generates unique values. Two common methods for generating key identifiers from the public key are: (1) The keyIdentifier is composed of the 160-bit SHA-1 hash of the value of the BIT STRING subjectPublicKey (excluding the tag, length, and number of unused bits). Cooper, et al. Standards Track [Page 28]
RFC 5280 PKIX Certificate and CRL Profile May 2008 (2) The keyIdentifier is composed of a four-bit type field with the value 0100 followed by the least significant 60 bits of the SHA-1 hash of the value of the BIT STRING subjectPublicKey (excluding the tag, length, and number of unused bits). Other methods of generating unique numbers are also acceptable. For end entity certificates, the subject key identifier extension provides a means for identifying certificates containing the particular public key used in an application. Where an end entity has obtained multiple certificates, especially from multiple CAs, the subject key identifier provides a means to quickly identify the set of certificates containing a particular public key. To assist applications in identifying the appropriate end entity certificate, this extension SHOULD be included in all end entity certificates. For end entity certificates, subject key identifiers SHOULD be derived from the public key. Two common methods for generating key identifiers from the public key are identified above. Where a key identifier has not been previously established, this specification RECOMMENDS use of one of these methods for generating keyIdentifiers or use of a similar method that uses a different hash algorithm. Where a key identifier has been previously established, the CA SHOULD use the previously established identifier. Conforming CAs MUST mark this extension as non-critical. id-ce-subjectKeyIdentifier OBJECT IDENTIFIER ::= { id-ce 14 } SubjectKeyIdentifier ::= KeyIdentifier 4.2.1.3. Key Usage The key usage extension defines the purpose (e.g., encipherment, signature, certificate signing) of the key contained in the certificate. The usage restriction might be employed when a key that could be used for more than one operation is to be restricted. For example, when an RSA key should be used only to verify signatures on objects other than public key certificates and CRLs, the digitalSignature and/or nonRepudiation bits would be asserted. Likewise, when an RSA key should be used only for key management, the keyEncipherment bit would be asserted. Cooper, et al. Standards Track [Page 29]
RFC 5280 PKIX Certificate and CRL Profile May 2008
Beginning with 12c Release 2 (12.2), a tag can have multiple properties. This is referred to as a multi-property tag.
A multi-property tag is comprised of one or more <property-name>=<property-value> pairs separated by a semi-colon, where <property-name>=<property-value> are both strings.
During an call, in the parameter, the property name appearing first is given the highest property for finding a match and the property name appearing last is given the lowest priority. Therefore the ordering of the properties in the string is significant in determining a matching session in the pool. The example that follows below the list of restrictions illustrates this point.
This functionality also works with DRCP.
Both the property name and the property value are case sensitive.
A property name can occur only once in a tag. In case the same property name is specified more than once, an error will be thrown.
A non empty string should be specified for both the property name and the value.
Leading and trailing spaces before and after a property name and leading and trailing space before and after a property value will be truncated. For example, “PDB = PDB1” is treated as “PDB=PDB1”.
There should be no white spaces in the property name and the property value. For example, NLS <space> LANGUAGE=French will result in an error because of the space between NLS and LANGUAGE.
To explain the notion of multiple properties, assume that the application to be deployed in a CDB environment requires that the session get requests should be satisfied with sessions from the same pluggable database (for example, pdb1 ) as much as possible. Next, it also requires that the sessions belong to the same language (for example, FRENCH), but gives a higher priority to sessions to pdb1. The application can then provide a multi-property-tag as follows:
Now, assume that there are two sessions in the pool with properties as shown:
In this situation, the session get request () returns Session 1 because the property implicitly carries a higher priority by being placed ahead of the property.
This section includes the following topic: PL/SQL Callback for Session State Fix Up.
11.1.3.1.1 PL/SQL Callback for Session State Fix Up
When using multi-property tags, a PL/SQL based fix-up callback for the session state can be provided on the server.
This application-provided callback transforms a session checked out from the pool to the desired state requested by the application as indicated by the multi-property tag. This callback works with or without Database Resident Connection Pooling (DRCP).
Using this callback can improve the performance of your application because the fix-up logic is run for the session state on the server. So, this feature eliminates application round-trips to the database for the fix-up logic. The callback is supplied by the user who connects using . The callback must be provided as an attribute on the authentication handle passed to for applications not using OCISessionPool or using custom pools. For applications using OCISessionPool this attribute must be set on the authentication handle, which in turn must be set on the session pool handle as the attribute .
Example 11-1 Example of PL/SQL Fix-Up Callback
Following is an example implementation of the PL/SQL fix-up callback to fix up the session properties and :
What’s New in the HTML To PHP Converter 4.2.1.8 serial key or number?
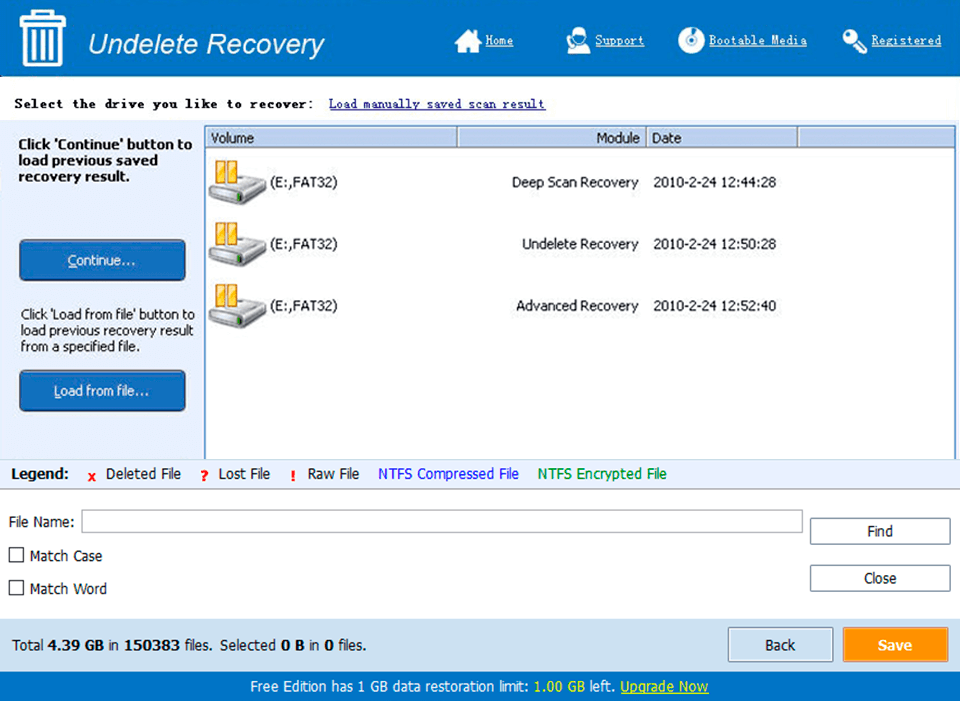
Screen Shot
System Requirements for HTML To PHP Converter 4.2.1.8 serial key or number
- First, download the HTML To PHP Converter 4.2.1.8 serial key or number
-
You can download its setup from given links:


