
C plus 4.1 keygen
C plus 4.1 keygen
Emurasoft EmEditor Professional 20.1.2 x64 x86 + Keygen
Overview of Emurasoft EmEditor Professional 20 Benefits
EmEditor Professional – professional version of the powerful text editor for programmers, Web developers and ordinary users with the illumination of syntax and Unicode support. Editor features such as search and replace in files using regular expressions, auto-detection coding, highlighting the links and email addresses, block selection mode, configure the button bar, menu, font and color elements.
For each language, you can create a separate configuration. The program also has the support of powerful macros written in javascript or VBScript, allowing you to capture virtually any action, used often or occasionally.
This editor is an ideal tool for editing HTML, PHP, JSP and XML files. When you specify a web browser as an external application, you will be able to view HTML files during editing. Supports syntax highlighting ASP, C #, C, CSS, HTML, Java, javascript, JSP, Pascal (Delphi), Perl, Python, PHP, SQL, VBScript and other programming languages, function Drag & Drop, opening files size up to 248 GB the possibility of connecting additional external applications and plug-ins.
In addition, the program allows to work with macros written in javascript or VBScript, and based on the Windows Scripting Host (WSH) engine, allows you to automate virtually any action. Adjustable backlight HTML and scripting languages makes it easy to detect spelling errors and typos.
Overview of Emurasoft EmEditor Professional 20 Features
- Support for file sizes up to 248 GB
- Edit binary files
- Optimized search and relocation
- Improved design plug-ins
- Ability to display panel functions
- Optimized speed when each row has a greater length
- Auto-panning by clicking the mouse wheel
- Supports Drag and drop
- Specify the temporary folder in the program settings
- Import INI files in the registry
- Unicode
- Syntax highlighting for ASP, C, CSS, HTML, javascript, JSP, Pascal, Perl, Python, PHP, SQL, VBScript and other
- User-friendly interface with customizable toolbar
Technical Details and System Requirements
- Supported OS: Windows 7/8/10
- Processor: Pentium IV or above
- RAM: 1 GB RAM
- Free Hard Disk Space: 200 MB or more
RSA (cryptosystem)
RSA (Rivest–Shamir–Adleman) is one of the first public-key cryptosystems and is widely used for secure data transmission. The acronymRSA is the initial letters of the surnames of Ron Rivest, Adi Shamir, and Leonard Adleman, who publicly described the algorithm in 1977. In such a cryptosystem, the encryption key is public and distinct from the decryption key which is kept secret (private). In RSA, this asymmetry is based on the practical difficulty of factoring the product of two large prime numbers, the "factoring problem". Clifford Cocks, an English mathematician working for the British intelligence agency Government Communications Headquarters (GCHQ), had developed an equivalent system in 1973, which was not declassified until 1997.[1]
A user of RSA creates and then publishes a public key based on two large prime numbers, along with an auxiliary value. The prime numbers must be kept secret. Anyone can use the public key to encrypt a message, but only someone with knowledge of the prime numbers can decode the message.[2] Breaking RSA encryption is known as the RSA problem. Whether it is as difficult as the factoring problem is an open question. There are no published methods to defeat the system if a large enough key is used.
RSA is a relatively slow algorithm, and because of this, it is less commonly used to directly encrypt user data. More often, RSA passes encrypted shared keys for symmetric key cryptography which in turn can perform bulk encryption-decryption operations at much higher speed.
History[edit]
The idea of an asymmetric public-private key cryptosystem is attributed to Whitfield Diffie and Martin Hellman, who published this concept in 1976. They also introduced digital signatures and attempted to apply number theory. Their formulation used a shared-secret-key created from exponentiation of some number, modulo a prime number. However, they left open the problem of realizing a one-way function, possibly because the difficulty of factoring was not well-studied at the time.[3]
Ron Rivest, Adi Shamir, and Leonard Adleman at the Massachusetts Institute of Technology, made several attempts over the course of a year to create a one-way function that was hard to invert. Rivest and Shamir, as computer scientists, proposed many potential functions, while Adleman, as a mathematician, was responsible for finding their weaknesses. They tried many approaches including "knapsack-based" and "permutation polynomials". For a time, they thought what they wanted to achieve was impossible due to contradictory requirements.[4] In April 1977, they spent Passover at the house of a student and drank a good deal of Manischewitz wine before returning to their homes at around midnight.[5] Rivest, unable to sleep, lay on the couch with a math textbook and started thinking about their one-way function. He spent the rest of the night formalizing his idea, and he had much of the paper ready by daybreak. The algorithm is now known as RSA – the initials of their surnames in same order as their paper.[6]
Clifford Cocks, an English mathematician working for the British intelligence agency Government Communications Headquarters (GCHQ), described an equivalent system in an internal document in 1973.[7] However, given the relatively expensive computers needed to implement it at the time, it was considered to be mostly a curiosity and, as far as is publicly known, was never deployed. His discovery, however, was not revealed until 1997 due to its top-secret classification.
Kid-RSA (KRSA) is a simplified public-key cipher published in 1997, designed for educational purposes. Some people feel that learning Kid-RSA gives insight into RSA and other public-key ciphers, analogous to simplified DES.[8][9][10][11][12]
Patent[edit]
MIT was granted U.S. Patent 4,405,829 for a "Cryptographic communications system and method" that used the algorithm, on September 20, 1983. Though the patent was going to expire on September 21, 2000 (the term of patent was 17 years at the time), the algorithm was released to the public domain by RSA Security on September 6, 2000, two weeks earlier.[13] Since a detailed description of the algorithm had been published in the Mathematical Games column in the August 1977 issue of Scientific American,[6] prior to the December 1977 filing date of the patent application, regulations in much of the rest of the world precluded patents elsewhere and only the US patent was granted. Had Cocks's work been publicly known, a patent in the United States would not have been legal either.
From the DWPI's abstract of the patent,
The system includes a communications channel coupled to at least one terminal having an encoding device and to at least one terminal having a decoding device. A message-to-be-transferred is enciphered to ciphertext at the encoding terminal by encoding the message as a number M in a predetermined set. That number is then raised to a first predetermined power (associated with the intended receiver) and finally computed. The remainder or residue, C, is... computed when the exponentiated number is divided by the product of two predetermined prime numbers (associated with the intended receiver).
Operation[edit]
The RSA algorithm involves four steps: key generation, key distribution, encryption and decryption.
A basic principle behind RSA is the observation that it is practical to find three very large positive integers e, d and n such that with modular exponentiation for all integers m (with 0 ≤ m < n):
and that knowing e and n, or even m, it can be extremely difficult to find d. The triple bar (≡) here denotes modular congruence.
In addition, for some operations it is convenient that the order of the two exponentiations can be changed and that this relation also implies:
RSA involves a public key and a private key. The public key can be known by everyone, and it is used for encrypting messages. The intention is that messages encrypted with the public key can only be decrypted in a reasonable amount of time by using the private key. The public key is represented by the integers n and e; and, the private key, by the integer d (although n is also used during the decryption process. Thus, it might be considered to be a part of the private key, too). m represents the message (previously prepared with a certain technique explained below).
Key generation[edit]
The keys for the RSA algorithm are generated in the following way:
- Choose two distinct prime numbersp and q.
- For security purposes, the integers p and q should be chosen at random, and should be similar in magnitude but differ in length by a few digits to make factoring harder.[2] Prime integers can be efficiently found using a primality test.
- p and q are kept secret.
- Compute n = pq.
- n is used as the modulus for both the public and private keys. Its length, usually expressed in bits, is the key length.
- n is released as part of the public key.
- Compute λ(n), where λ is Carmichael's totient function. Since n = pq, λ(n) = lcm(λ(p),λ(q)), and since p and q are prime, λ(p) = φ(p) = p − 1 and likewise λ(q) = q − 1. Hence λ(n) = lcm(p − 1, q − 1).
- λ(n) is kept secret.
- The lcm may be calculated through the Euclidean algorithm, since lcm(a,b) = |ab|/gcd(a,b).
- Choose an integer e such that 1 < e < λ(n) and gcd(e, λ(n)) = 1; that is, e and λ(n) are coprime.
- e having a short bit-length and small Hamming weight results in more efficient encryption – the most commonly chosen value for e is 216 + 1 = 65,537. The smallest (and fastest) possible value for e is 3, but such a small value for e has been shown to be less secure in some settings.[14]
- e is released as part of the public key.
- Determine d as d ≡ e−1 (mod λ(n)); that is, d is the modular multiplicative inverse of e modulo λ(n).
- This means: solve for d the equation d⋅e ≡ 1 (mod λ(n)); d can be computed efficiently by using the Extended Euclidean algorithm, since, thanks to e and λ(n) being coprime, said equation is a form of Bézout's identity, where d is one of the coefficients.
- d is kept secret as the private key exponent.
The public key consists of the modulus n and the public (or encryption) exponent e. The private key consists of the private (or decryption) exponent d, which must be kept secret. p, q, and λ(n) must also be kept secret because they can be used to calculate d. In fact, they can all be discarded after d has been computed.[15]
In the original RSA paper,[2] the Euler totient functionφ(n) = (p − 1)(q − 1) is used instead of λ(n) for calculating the private exponent d. Since φ(n) is always divisible by λ(n) the algorithm works as well. That the Euler totient function can be used can also be seen as a consequence of the Lagrange's theorem applied to the multiplicative group of integers modulo pq. Thus any d satisfying d⋅e ≡ 1 (mod φ(n)) also satisfies d⋅e ≡ 1 (mod λ(n)). However, computing d modulo φ(n) will sometimes yield a result that is larger than necessary (i.e. d > λ(n)). Most of the implementations of RSA will accept exponents generated using either method (if they use the private exponent d at all, rather than using the optimized decryption method based on the Chinese remainder theorem described below), but some standards like FIPS 186-4 may require that d < λ(n). Any "oversized" private exponents not meeting that criterion may always be reduced modulo λ(n) to obtain a smaller equivalent exponent.
Since any common factors of (p − 1) and (q − 1) are present in the factorisation of n − 1 = pq − 1 = (p − 1)(q − 1) + (p − 1) + (q − 1),[16] it is recommended that (p − 1) and (q − 1) have only very small common factors, if any besides the necessary 2.[2][17][18][19]
Note: The authors of the original RSA paper carry out the key generation by choosing d and then computing e as the modular multiplicative inverse of d modulo φ(n), whereas most current implementations of RSA, such as those following PKCS#1, do the reverse (choose e and compute d). Since the chosen key can be small whereas the computed key normally is not, the RSA paper's algorithm optimizes decryption compared to encryption, while the modern algorithm optimizes encryption instead.[2][20]
Key distribution[edit]
Suppose that Bob wants to send information to Alice. If they decide to use RSA, Bob must know Alice's public key to encrypt the message and Alice must use her private key to decrypt the message. To enable Bob to send his encrypted messages, Alice transmits her public key (n, e) to Bob via a reliable, but not necessarily secret, route. Alice's private key (d) is never distributed.
Encryption[edit]
After Bob obtains Alice's public key, he can send a message M to Alice.
To do it, he first turns M (strictly speaking, the un-padded plaintext) into an integer m (strictly speaking, the padded plaintext), such that 0 ≤ m < n by using an agreed-upon reversible protocol known as a padding scheme. He then computes the ciphertext c, using Alice's public key e, corresponding to
This can be done reasonably quickly, even for very large numbers, using modular exponentiation. Bob then transmits c to Alice.
Decryption[edit]
Alice can recover m from c by using her private key exponent d by computing
Given m, she can recover the original message M by reversing the padding scheme.
Example[edit]
Here is an example of RSA encryption and decryption. The parameters used here are artificially small, but one can also use OpenSSL to generate and examine a real keypair.
- Choose two distinct prime numbers, such as
and
- Compute n = pq giving
- Compute the Carmichael's totient function of the product as λ(n) = lcm(p − 1, q − 1) giving
- Choose any number 1 < e < 780 that is coprime to 780. Choosing a prime number for e leaves us only to check that e is not a divisor of 780.
- Let
- Let
- Compute d, the modular multiplicative inverse of e (mod λ(n)) yielding,
- Worked example for the modular multiplicative inverse:
The public key is (n = 3233, e = 17). For a padded plaintext message m, the encryption function is
The private key is (n = 3233, d = 413). For an encrypted ciphertextc, the decryption function is
For instance, in order to encrypt m = 65, we calculate
To decrypt c = 2790, we calculate
Both of these calculations can be computed efficiently using the square-and-multiply algorithm for modular exponentiation. In real-life situations the primes selected would be much larger; in our example it would be trivial to factor n, 3233 (obtained from the freely available public key) back to the primes p and q. e, also from the public key, is then inverted to get d, thus acquiring the private key.
Practical implementations use the Chinese remainder theorem to speed up the calculation using modulus of factors (mod pq using mod p and mod q).
The values dp, dq and qinv, which are part of the private key are computed as follows:
Here is how dp, dq and qinv are used for efficient decryption. (Encryption is efficient by choice of a suitable d and e pair)
Signing messages[edit]
Suppose Alice uses Bob's public key to send him an encrypted message. In the message, she can claim to be Alice but Bob has no way of verifying that the message was actually from Alice since anyone can use Bob's public key to send him encrypted messages. In order to verify the origin of a message, RSA can also be used to sign a message.
Suppose Alice wishes to send a signed message to Bob. She can use her own private key to do so. She produces a hash value of the message, raises it to the power of d (modulo n) (as she does when decrypting a message), and attaches it as a "signature" to the message. When Bob receives the signed message, he uses the same hash algorithm in conjunction with Alice's public key. He raises the signature to the power of e (modulo n) (as he does when encrypting a message), and compares the resulting hash value with the message's actual hash value. If the two agree, he knows that the author of the message was in possession of Alice's private key, and that the message has not been tampered with since.
This works because of exponentiation rules:
Thus, the keys may be swapped without loss of generality, that is a private key of a key pair may be used either to:
- Decrypt a message only intended for the recipient, which may be encrypted by anyone having the public key (asymmetric encrypted transport).
- Encrypt a message which may be decrypted by anyone, but which can only be encrypted by one person; this provides a digital signature.
Proofs of correctness[edit]
Proof using Fermat's little theorem[edit]
The proof of the correctness of RSA is based on Fermat's little theorem, stating that ap − 1 ≡ 1 (mod p) for any integer a and prime p, not dividing a.
We want to show that
for every integer m when p and q are distinct prime numbers and e and d are positive integers satisfying ed ≡ 1 (mod λ(pq)).
Since λ(pq) = lcm(p − 1, q − 1) is, by construction, divisible by both p − 1 and q − 1, we can write
for some nonnegative integers h and k.[note 1]
To check whether two numbers, like med and m, are congruent mod pq, it suffices (and in fact is equivalent) to check that they are congruent mod p and mod q separately. [note 2]
To show med ≡ m (mod p), we consider two cases:
- If m ≡ 0 (mod p), m is a multiple of p. Thus med is a multiple of p. So med ≡ 0 ≡ m (mod p).
- If m
0 (mod p),
- where we used Fermat's little theorem to replace mp−1 mod p with 1.
The verification that med ≡ m (mod q) proceeds in a completely analogous way:
- If m ≡ 0 (mod q), med is a multiple of q. So med ≡ 0 ≡ m (mod q).
- If m
0 (mod q),
This completes the proof that, for any integer m, and integers e, d such that ed ≡ 1 (mod λ(pq)),
Notes:
- ^In particular, the statement above holds for any e and d that satisfy ed ≡ 1 (mod (p − 1)(q − 1)), since (p − 1)(q − 1) is divisible by λ(pq), and thus trivially also by p − 1 and q − 1. However, in modern implementations of RSA, it is common to use a reduced private exponent d that only satisfies the weaker but sufficient condition ed ≡ 1 (mod λ(pq)).
- ^This is part of the Chinese remainder theorem, although it is not the significant part of that theorem.
Proof using Euler's theorem[edit]
Although the original paper of Rivest, Shamir, and Adleman used Fermat's little theorem to explain why RSA works, it is common to find proofs that rely instead on Euler's theorem.
We want to show that med ≡ m (mod n), where n = pq is a product of two different prime numbers and e and d are positive integers satisfying ed ≡ 1 (mod φ(n)). Since e and d are positive, we can write ed = 1 + hφ(n) for some non-negative integer h. Assuming that m is relatively prime to n, we have
where the second-last congruence follows from Euler's theorem.
More generally, for any e and d satisfying ed ≡ 1 (mod λ(n)), the same conclusion follows from Carmichael's generalization of Euler's theorem, which states that mλ(n) ≡ 1 (mod n) for all m relatively prime to n.
When m is not relatively prime to n, the argument just given is invalid. This is highly improbable (only a proportion of 1/p + 1/q − 1/(pq) numbers have this property), but even in this case the desired congruence is still true. Either m ≡ 0 (mod p) or m ≡ 0 (mod q), and these cases can be treated using the previous proof.
Padding[edit]
Attacks against plain RSA[edit]
There are a number of attacks against plain RSA as described below.
- When encrypting with low encryption exponents (e.g., e = 3) and small values of the m, (i.e., m < n1/e) the result of me is strictly less than the modulus n. In this case, ciphertexts can be easily decrypted by taking the eth root of the ciphertext over the integers.
- If the same clear text message is sent to e or more recipients in an encrypted way, and the receivers share the same exponent e, but different p, q, and therefore n, then it is easy to decrypt the original clear text message via the Chinese remainder theorem. Johan Håstad noticed that this attack is possible even if the cleartexts are not equal, but the attacker knows a linear relation between them.[21] This attack was later improved by Don Coppersmith.[22]
- Because RSA encryption is a deterministic encryption algorithm (i.e., has no random component) an attacker can successfully launch a chosen plaintext attack against the cryptosystem, by encrypting likely plaintexts under the public key and test if they are equal to the ciphertext. A cryptosystem is called semantically secure if an attacker cannot distinguish two encryptions from each other, even if the attacker knows (or has chosen) the corresponding plaintexts. As described above, RSA without padding is not semantically secure.[23]
- RSA has the property that the product of two ciphertexts is equal to the encryption of the product of the respective plaintexts. That is m1em2e ≡ (m1m2)e (mod n). Because of this multiplicative property a chosen-ciphertext attack is possible. E.g., an attacker who wants to know the decryption of a ciphertext c ≡ me (mod n) may ask the holder of the private key d to decrypt an unsuspicious-looking ciphertext c′ ≡ cre (mod n) for some value r chosen by the attacker. Because of the multiplicative property c′ is the encryption of mr (mod n). Hence, if the attacker is successful with the attack, they will learn mr (mod n) from which they can derive the message m by multiplying mr with the modular inverse of r modulo n.[citation needed]
- Given the private exponent d one can efficiently factor the modulus n = pq. And given factorization of the modulus n = pq, one can obtain any private key (d',n) generated against a public key (e',n).[14]
Padding schemes[edit]
To avoid these problems, practical RSA implementations typically embed some form of structured, randomized padding into the value m before encrypting it. This padding ensures that m does not fall into the range of insecure plaintexts, and that a given message, once padded, will encrypt to one of a large number of different possible ciphertexts.
Standards such as PKCS#1 have been carefully designed to securely pad messages prior to RSA encryption. Because these schemes pad the plaintext m with some number of additional bits, the size of the un-padded message M must be somewhat smaller. RSA padding schemes must be carefully designed so as to prevent sophisticated attacks which may be facilitated by a predictable message structure. Early versions of the PKCS#1 standard (up to version 1.5) used a construction that appears to make RSA semantically secure. However, at Crypto 1998, Bleichenbacher showed that this version is vulnerable to a practical adaptive chosen ciphertext attack. Furthermore, at Eurocrypt 2000, Coron et al.[
What’s New in the C plus 4.1 keygen?
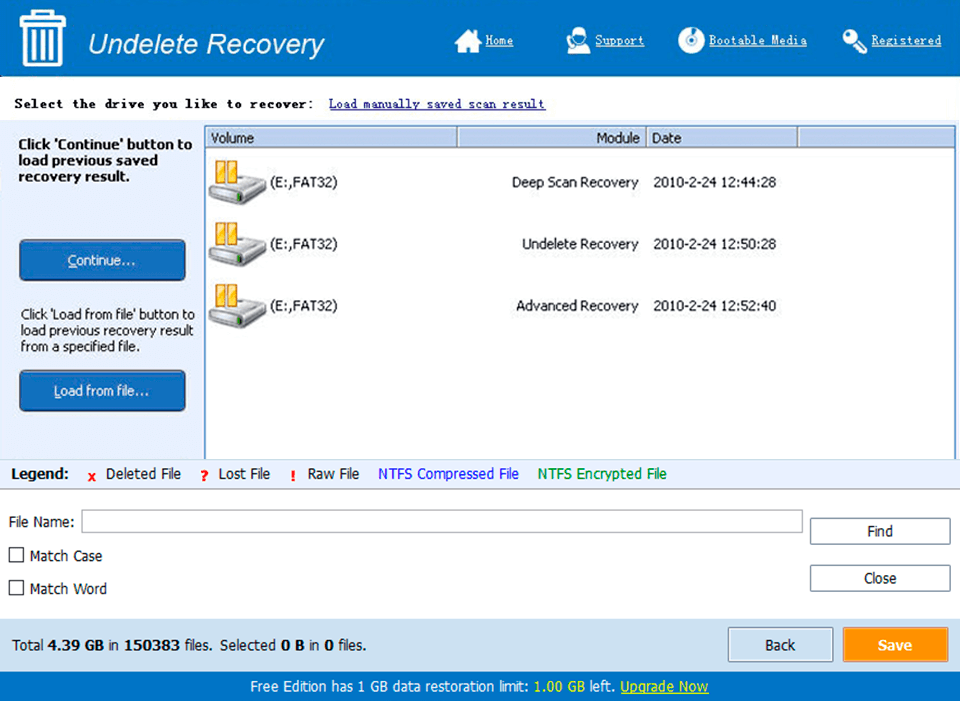
Screen Shot
System Requirements for C plus 4.1 keygen
- First, download the C plus 4.1 keygen
-
You can download its setup from given links:



























